I have been working with Symantec Data Loss Prevention (DLP) ever since Symantec acquired Vontu. This technology has evolved a lot over time, but there is a lot more beyond. I always quote “The true enablement of DLP begins after the infrastructure deployment”, and in this blog, I aim to elaborate more.
For most organizations, the infrastructure deployment involved can take from days to weeks, but execution of a DLP business strategy likely runs for months to years. One of the key goals of a DLP program is to implement some data governance measures, and this is not possible without gaining visibility into how data is leveraged within an organization. Below are some of the key aspects that any organization must consider beyond the infrastructure implementation:
1. INCIDENT MANAGEMENT WORKFLOW
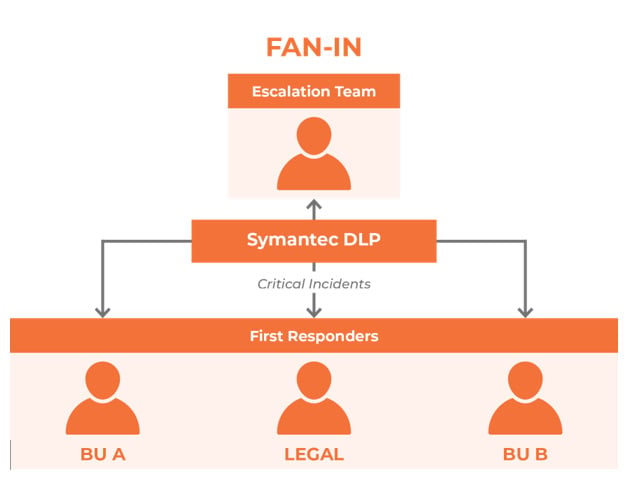
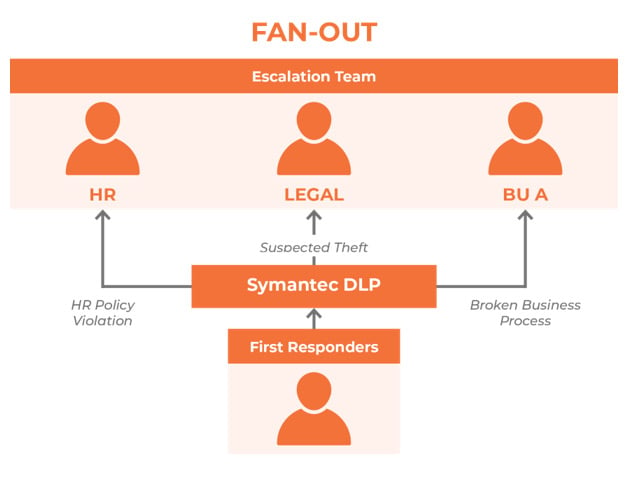
A typical DLP scan (for e.g. PCI scan) could generate thousands of incidents. These could involve ‘True Positives’ as well as ‘False Positives’, and somebody needs to review these incidents to determine the status. However, it is not always possible for an Incident Analyst to make the decision, as it could require additional eyes. An Incident Management Workflow solves this challenge by formulating a defined strategy. Some of the known strategies around DLP workflow involve:
- Fan In – This Incident Management Strategy suitable for organizations where independent business units are actively involved and motivated to participate in the DLP program. They perform the first level review of incidents for their business unit and flag potential ‘True Positives’ for further analysis by the DLP team. In my experience, ‘Fan In’ has not been the most successful strategy, as it requires significant billable hours invested by a business unit into somethingwhich is not their Key Performance Indicator (KPI).
- Fan Out – This strategy is the most commonly adopted strategy, where the DLP team performs initial incident analysis, and flags /escalates potential ‘True Positives’ to the appropriate business units. This requires limited investment of billable hours from the business unit, thus making it possible to have them involved.
- Hybrid (Fan In & Out) – Depending on an organization’s structure and the involvement of business units, it may be possible to set up a hybrid incident management structure. The downside with this strategy is that there is no single point of ownership, but it can be mitigated by defining a clear set of responsibilities /KPI’s.
1. DLP Stakeholders
A typical DLP program cannot be successful without constant involvement and direction. Hence, it is imperative to have the following roles defined:
- DLP Steering Committee – The DLP steering committee is the ‘North star’ of the DLP program which reviews the risk landscape and makes appropriate decisions for directing the program. This involves resources like the CIO, CTO, Information Security team, Business stakeholders etc.
- DLP Program Manager – I would term this person as ‘Champion of the DLP Program’ since it is his/her job to keep the appropriate resources involved and drive DLP in a certain direction. Data Loss Prevention cannot be achieved with just one solution but is a blended combination of multiple strategies/solutions like DLP, Classification, Encryption, Identity and Access Management etc. The DLP Program Manager acts as a bridge between the Incident Management Team and the Steering Committee, thus ensuring the appropriate risk reduction measures are implemented over time.
2. Ongoing Data Analysis
The criticality of many data types is time-bound, and most importantly the definition of critical data is constantly evolving in any organization. I define critical data with this question “What is the impact of this data leaking outside the organization?”. The answer determines if this data may be a candidate for DLP or not. This ongoing data analysis is only possible through continuous workshops and involvement with business units, something the DLP Program Manager is responsible for driving.
In conclusion, the technology infrastructure deployment of DLP is just a starting point. While we provide customers with all the necessary direction towards business enablement, this is something which happens over a much longer period. Please feel free to reach out to Insentra should you need assistance with the ongoing business enablement of DLP.










