On a recent engagement deploying Windows Virtual Desktop (WVD) for a customer who leveraged OKTA as their Identity Provider (IDP), we ran into a challenge where the WVD client was caching user credentials (by design), resulting in a situation where on the first authentication, OKTA would prompt for multi-factor authentication, however once validated, the WVD client would never request authentication again, resulting in a rather large security concern for the customer who had a mandate of multi-factor authentication for all external access attempts.
We can get pretty close to meeting that mandate by leveraging Azure Active Conditional Access Policies to assist in setting the sign-in frequency interval to 1 hour. The sign-in frequency defines the time before a user is asked to sign in again when attempting to access a cloud application.
We can leverage a combination of OKTA for identity in conjunction with Microsoft Azure Conditional Access Policies for application control, ensuring that we apply our specific control requirements only to the appropriate enterprise application, in this case, Windows Virtual Desktop (and client).
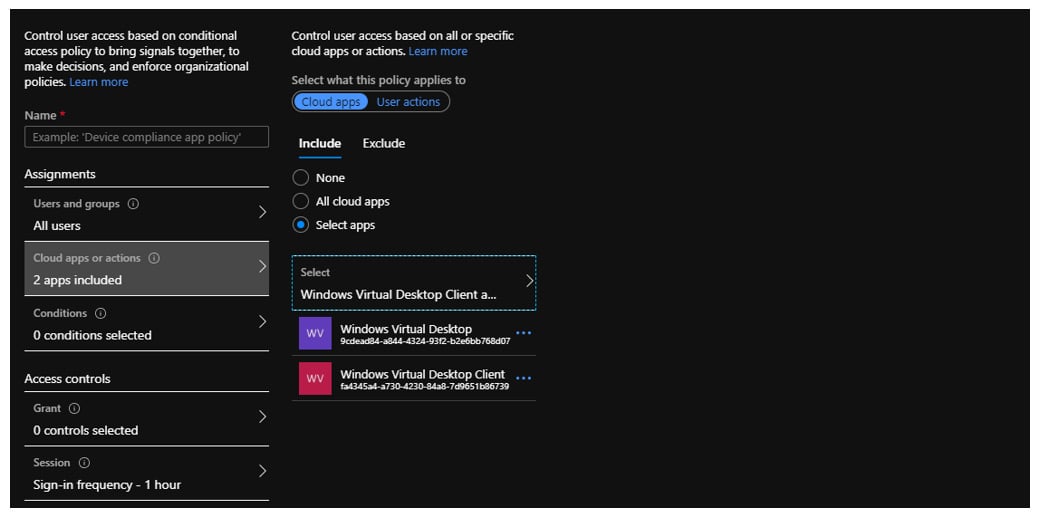
Specifically, the policy is configured as follows:
- Applies to all users
- Applies to specific cloud apps (WVD)
- Has a single session control defined (Sign-in frequency is set to 1 hour)
Combined with the usual power of Conditional Access Policies, you can get extremely fine-grained. What’s even cooler is that you can still wrap these controls around 3rd party IDP’s such as OKTA and leverage the best of both worlds
If you have enough licencing to be running WVD, there is a good chance you have enough to protect it via Microsoft Azure Conditional Access at no extra cost.










