A laptop was lost or stolen, files were copied through a breach, or an incorrect file was simply attached to an email – things no IT Professional ever wants to hear. The need to know where, how and who is accessing important company data is an issue as old as it is ever-changing.
In the past, tight physical security protocols protected paper files in cabinets and knowing who held the key and who accessed them was done entirely through manpower. In the digital world, a hard copy is simply one of the many manifestations of data, but digital copies are harder to safeguard and keep track of. As such, Data Loss Prevention (DLP) is more important now than ever.
Understanding how to protect information and how to restrict access because of the myriad of ways data can be accessed can quickly become overwhelming. How do companies ensure only the right people are accessing sensitive data no matter where that data is?
Azure Information Protection (AIP) addresses this need as a cloud-based solution helping to classify, protect through encryption, and track access to labeled documents and emails.
DLP vs AIP
What does AIP have to do with DLP? It’s one of many tools that Microsoft delivers to help companies protect their data.
Microsoft’s Office 365 Data Loss Prevention offering by itself is focused on compliance standards and regulations and informing administrators when information such as Personally Identifiable Information (PII) is found or shared in an environment.
An example would be a PCI-compliant company monitoring to ensure no credit card numbers are saved in SharePoint Online (SPO). The DLP policy would monitor SPO and, if CC numbers were found, restrict access until the original editor removes them or the file itself is deleted. In this scenario, DLP is protecting and monitoring information after it has been created within the Office 365 tenant.
Azure Information Protection protects individual files (or emails!) no matter where they live or are sent. The AIP protections used to apply the classification, protections, and markings to the file are called labels.
“Labels? You mean the things in my filing cabinet?”
No, and it’s going to get a little confusing because in AIP they’re just called “labels.”
Applying a label can be done during the initial creation, afterward during an edit, or even using the client in the file explorer. The bonus of labels is they allow for classification of the type of business-critical information contained in a document. I’ve always thought it was easiest to imagine files and emails protected by AIP to be “wrapped”, meaning the file is encrypted and AIP is the gatekeeper. Once a file is wrapped, there is an Access Control List (ACL) defined by the AIP label identifying who can do what to the file.
There are additional options as well. For example, a setting whether the file can be accessed offline or an automatic expiration date. What happens to the file regarding access, markings, expiration and protection all depends on the applied label. Each time a file is opened, it will check in with Azure to verify if the user is authorized to do so. This ensures the data is protected no matter where it happens to be resting.
After a document has been protected, it is possible to track who has accessed the document, been denied access and a rough geographical location of where it was accessed. This goes together with the capability to revoke access to the document. Once access is revoked, no one can get back into the data except the user who applied the protections or a delegated administrator.
“Wait, what do you mean that it depends on the label?”
Yep, that’s correct, and there can be a lot of labels if you choose to create them. As I’ve mentioned previously, labels are what AIP uses to assign protections stated. Labels are assigned to a policy and can only be assigned to one policy, then policies are assigned to users or distribution groups.
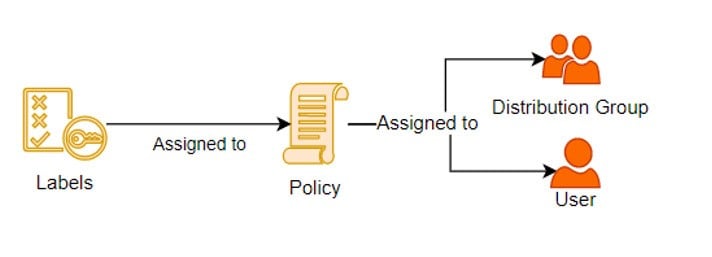
“Global” labels can be created and added to the native Global policy (e.g. company confidential) and applied to everyone in a tenant. Additionally, department-specific labels tailored explicitly for what protections they require will only be assigned to the policy delivering them to the intended users. There is even the ability to allow the creation of custom labels by users for specific one-off situations.
This capability is built directly into Office Suite, as long as you’re using the latest version. A standalone downloadable “Azure Information Protection” client application can also be installed on each user’s machine to utilize the labels they are assigned. The client also grants the ability to assign AIP labels while using file explorer, even to non-office documents such as a PDF file. This means you can protect almost any file!
For mobile access, there is an AIP viewer app which enables Android and Apple systems to open AIP protected documents. The Outlook Mobile app has the built-in ability to open AIP protected emails. Protected emails can’t be opened by some native email applications and will require the installation of the viewer or the Outlook App. For a full list of supported OS/ Applications, please refer to Microsoft documentation.
If you want to dive into the technical side of Azure Information Protection, check out this episode of Late Night Brew where I talk to Hugh and Lee about how AIP works. Feel free to reach out to Insentra if you need assistance on utilizing AIP in your organization.










