Multi-Factor Authentication (MFA) is one of the low hanging fruits when it comes to protecting your identity and securing technologies such as Citrix Virtual Apps and Desktops.
Disturbingly, we still see many environments which are not securing themselves; still leveraging a single factor, basic Active Directory username and password for authentication. This is a significant security hole and should be the highest priority item on your list of projects/outcomes to implement ASAP.

In the current landscape, the cost is not a factor any longer given there are several entitlements included in the technology stacks most customers are consuming. Additionally, Fear of Change (or FoC) can no longer be used as an argument as consumer applications and services have been forcing MFA methodology for years. Not seeing this in the enterprise raises more flags than the requirement for it, both from security savvy individuals, through to the everyday consumer. Who do you know who can access a mobile banking application without being challenged for additional verification that you are indeed who you appear to be?
This post outlines two options available to almost all customers. Of course, there are additional paths and options, but at typically next to no additional cost, these are the areas we focus on.
SOLUTION 1: AZURE ACTIVE DIRECTORY
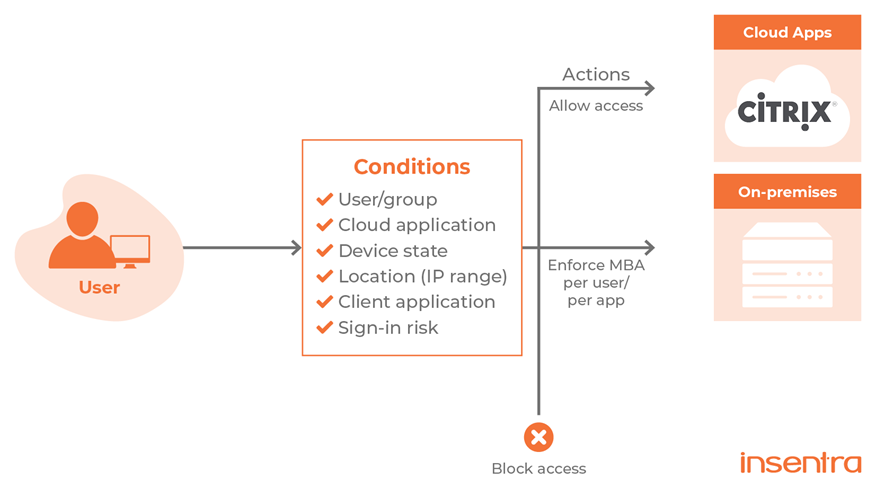
Azure Active Directory underpins Office 365 services. If you are an Office 365 customer, you have Azure Active Directory available to you. There are multiple tiers of licencing and capability for Azure Active Directory however, some recent changes by Microsoft now means any Microsoft customer using a subscription of a commercial online service such as Azure, Office 365, Dynamics and Power Platform can enable SSO for all their cloud apps, even with Azure AD Free. This means that if you have any form of commercial entitlement, you can integrate your Citrix environment with Azure Active Directory and achieve either basic multi-factor authentication protection or a more enhanced Conditional Access driven identity protection mechanism – should you be entitled to it.
Leveraging Azure Active Directory typically requires handoff via SAML authentication to Microsoft, from either your existing Citrix StoreFront, Citrix ADC Gateway or Citrix Cloud Workspace. To support the translation of SAML to a method which Windows understands, Citrix provides the Federated Authentication Service which issues a certificate for the user and performs a virtual smart card logon to the Windows endpoint. Conversely, the same process and requirements exist should you consume a 3rd party IDP like OKTA in place of Azure Active Directory.
Alternatively, Azure MFA can be leveraged by using the Network Policy Server (NPS extensions), however this is counter-intuitive to those with conditional access requirements.
SOLUTION 2: CITRIX TIME-BASED ONE-TIME PASSWORD
Citrix Cloud (Workspace) and Citrix Application Delivery Controllers (ADC) both offer a native form of Citrix Driven Time-based One-time Password (TOTP) second-factor authentication. This capability is for those users running Active Directory as their primary identity source and are looking to add some additional security to their access solutions where 3rd party providers are not an option (such as Microsoft, OKTA, DUO etc).

For Citrix ADC deployments, this functionality is included with an Advanced or Premium Licence and falls under nFactor (AAA) authentication policies.
For Citrix Cloud-based deployments, the TOTP solution is delivered directly from the Cloud (Citrix Workspace) and can leverage the likes of Google Authentication, Microsoft Authenticator, Citrix SSO mobile apps. The capability is included in the Workspace Service.
SUMMARY
Multi-Factor Authentication is no longer a “nice to have” solution. Identity theft is real and it is common. It is critical to hardening your remote access systems (all systems for that matter regardless of location) and protecting your users’ identity. With the increased flexible working arrangements currently in play, and the entitlements available to almost every customer, now is the time to close at least one weak point in the environment with some very easy wins.










