
Table of Contents
Why is Zero Trust so important?
How does Zero Trust Security work?
What are the Principles of Zero Trust?
What are the Pillars of Zero Trust Architecture?
What Impact will Zero Trust Security have on User Experience?
What is the Cost Impact of Zero Trust Security?
How to begin your Zero Trust Security Implementation
How to develop a Long Term Zero Trust Security Strategy Roadmap in the Microsoft Ecosystem
What does a Zero Trust Maturity Model look like?
How Insentra can help with your Zero Trust Security Strategy
INTRODUCTION
If you live in the Information Technology industry (or just visit from time to time) then you are fully aware of the rise in cybercrime over the last decade. Even those outside of the industry have heard about many high-profile breaches which have made headline news around the world. This trend shows no sign of slowing and, in fact, the great landscape continues to rapidly evolve.
To combat the threat, companies have become hyper focused on cybersecurity. Terms like Zero Trust Architecture, Zero Trust Framework, Zero Trust Security, Zero Trust Model and Zero Trust Network are being used repeatedly. Most major security vendors, cloud platforms, management suites, networking companies and identity and access management providers are now integrating Zero Trust solutions into their existing security components and offerings.
Sometimes there are buzzwords just for the sake of buzzwords, but other times, such as this one, important sounding words or phrases can be valuable and have merit. In this guide we will explore why the Zero Trust concept/model/framework is essential, its core principles, the pillars it’s built upon, the impact it can have on your business and how to begin to incrementally incorporate Zero Trust approaches into your existing architecture.
A QUICK NOTE ON TERMINOLOGY
While most of the core concepts of Zero Trust Architecture are universally agreed upon, you will see various interpretations with subtle differences depending on which article you read. There may be different names for certain aspects or a slightly differing number of defined pillars. These variances are only minor and do not constitute a major deviation in the intent-of or approach-to implementation of a Zero Trust Security Model.
This paper focuses on Microsoft’s definition of Zero Trust Architecture and the related offerings available across the Microsoft 365 and Azure platforms at the time of this writing. While there are many good solutions on the market, organisations already consuming Microsoft cloud services may experience an easier time implementing the Zero Trust principles as the required products are already present and integrated into the platform.
It is also worth pointing out some organisations choose to implement security tools using a best-in-breed approach leveraging analysis trends from trusted third parties such as Gartner Magic Quadrants. While this is certainly a valid approach, and you may see small gains in various feature sets, there is an overall loss of visibility and control when compared to a single platform managing the end-end solution of identity, applications, data, threat protection and device management. Yes, you are theoretically putting all your eggs in one basket, but you are certainly not alone. Many global organisations are doing just this and achieving successful outcomes. As is often the case, these decisions come down to the delicate balancing act of managing risk for your organisation.
WHAT IS ZERO TRUST?
Zero Trust is a philosophy first invented by John Kindervag when he was a principal analyst at Forrester Research. His famous quote is: “When every user, packet, network interface and device is untrusted, protecting assets becomes simple.” This ground-breaking concept was contrary to the industry-standard approach at the time which believed devices could be trusted by default and the network perimeter was sufficient to ward off any unsanctioned access to corporate resources.
Prior to Kindervag’s observation, the approach to network security was known as the “Trust but Verify” method, where trust was the default posture. Once a person’s identity had been validated, administrators would allow users unfettered access to the network. It also meant the endpoint the user was operating from would have unrestricted access to the entire infrastructure.
Zero Trust is effectively taking the opposite position and equates to a posture of “Never Trust, Always Verify”. The Trust but Verify approach can be considered fundamentally flawed if the primary goal is to prevent a compromise. By flipping this concept on its head and instead saying a device is untrusted by default, then protecting against a compromise becomes much more effective.
To be fair, let’s first understand how the old philosophy became commonplace.
Once upon a time, all the valuable data in the kingdom was stored in a beautiful walled garden and was protected by a mighty firewall. To access the data, a user had to be inside the walled garden, plugged into a known network port and had to know their password.
The armour of this strategy eventually began to crack when the bad actors realised people were inherently gullible, inquisitive and could be easily persuaded to click on things they shouldn’t. Once clicked, they could voluntarily install malware on their trusted devices thereby allowing uninvited guests inside the walled garden to pillage and plunder.
WHY IS ZERO TRUST SO IMPORTANT?

The proliferation of cloud computing in the early 2000s was a game-changer. It brought great benefits by relieving organisations from the burden of having to continuously manage infrastructure and allowed them to enjoy the fruits of modern and always up-to-date line of business applications through the Software as a Service (SaaS) model. From a security perspective, however, things became more complicated very quickly. Now, sensitive corporate data has left the building and is resident in someone else’s network being accessed over the internet (aka the most untrusted network ever!).
Enter Mobility
In addition to data now being distributed across cloud datacentres, technological advancements have equipped users to be more mobile. If the data lives in the cloud, then why should the user be bound to an office building to access it? People are more productive when they can work from home, on the road, in a hotel, at a coffee shop or even at the gym. This was embraced by organisations since more productive workers equal more output and more profits for the business. So now we have users accessing sensitive corporate data from anywhere using any device at any time over the most untrusted network ever… What could go wrong?
More Sophisticated Attacks
Cloud computing and mobility revolutionised how businesses operate by reducing their infrastructure footprint with cutting-edge cloud-based SaaS applications and empowering knowledge workers to be more productive by consuming data from anywhere.
However, all this innovation came at a cost. It provided more opportunities for hackers to revolutionise how they can attack organisations for profit. The perceived small attack surface of yesteryear (the walled garden) has now expanded exponentially to the far reaches of the globe.
Money is the ultimate motivator and the bad actors haven’t been resting on their laurels. Rather, they have been advancing alongside the rest of the industry. With more modern threats come more evolved attacks such as spear phishing and ransomware. The attackers graduated from just creating short-term havoc to holding data hostage and employing clandestine spying tactics to execute very targeted and well-planned attacks which are much more devastating and costly to businesses.
Identity, Identity, Identity
Did you ever hear the real estate expression “Location, Location, Location”? It means more than anything else, the location of a property determines its value. Well in a Trust but Verify approach, identity, more than anything else determines access to resources. A credential (username and password) is the only information required to impersonate an identity. If the identity verifies the trust, then the identity is the key to the kingdom. Whether it is to use the identity to steal data, lay malware, encrypt data for ransom or gather exploitable intelligence from the birds-eye-view of an insider, identity theft has become the number one manner organisations have been breached in the current day. For this reason, identity has been coined the “new perimeter” or “new security boundary.”
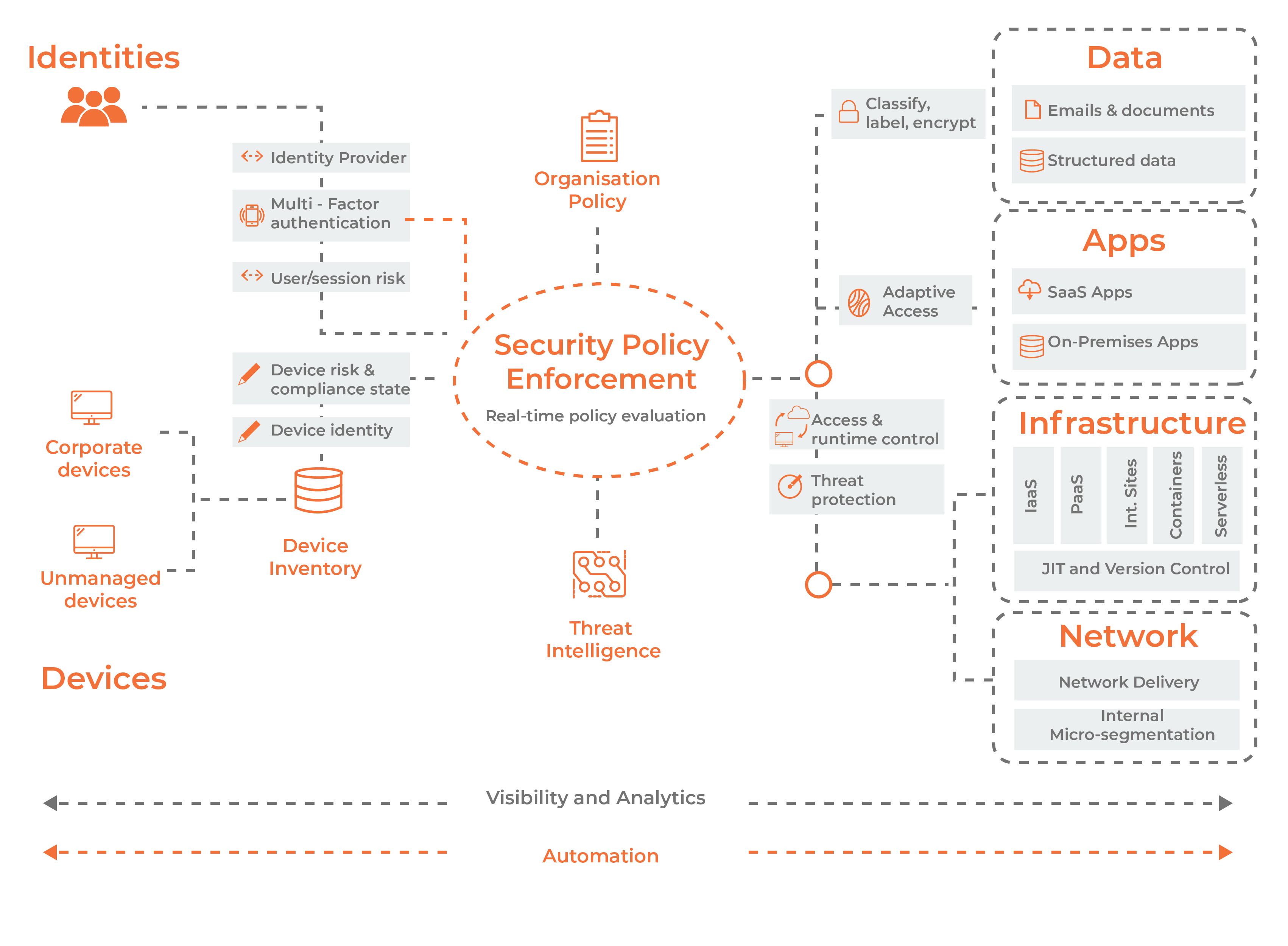
HOW DOES ZERO TRUST SECURITY WORK?
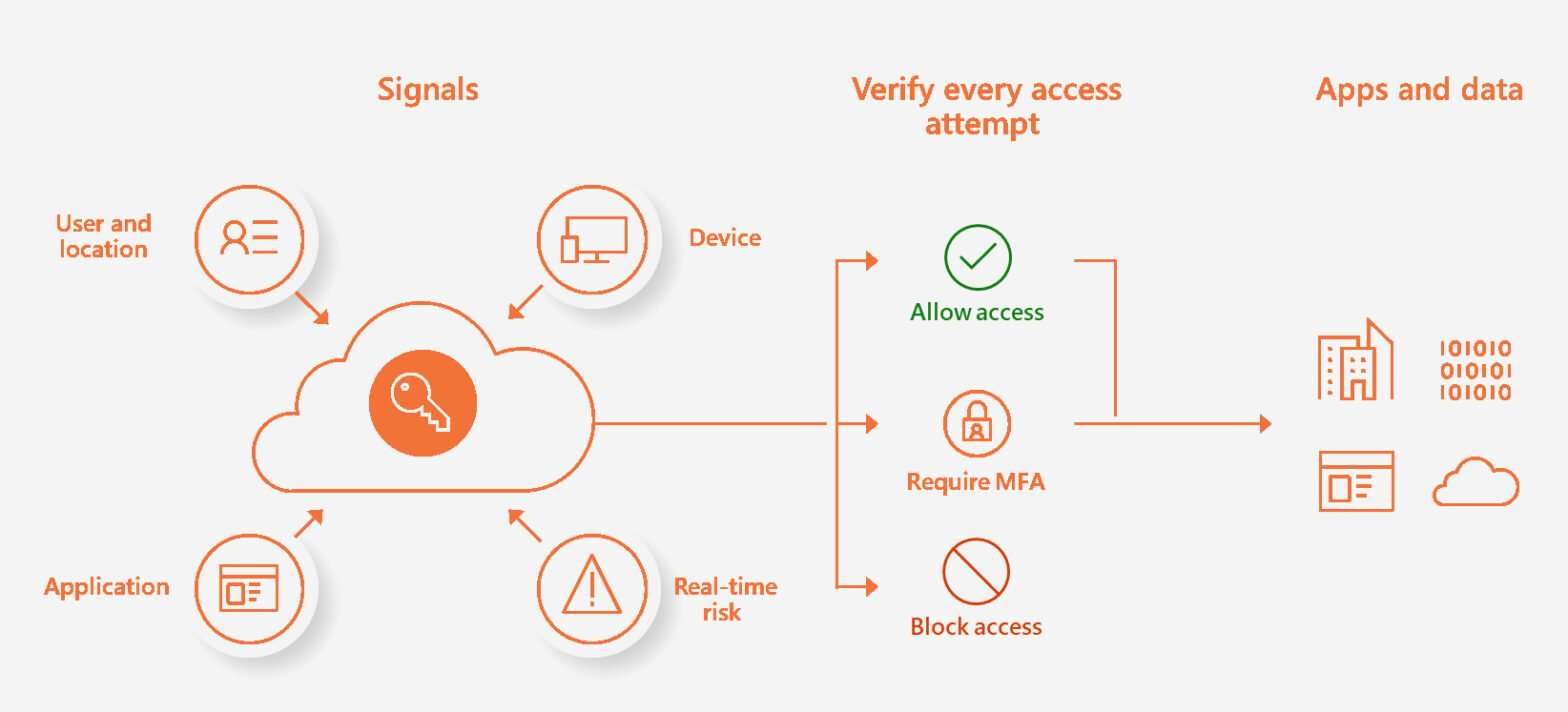
In a Zero Trust Security Model we treat every access attempt the same, regardless of where it originated. Don’t blindly trust a device because it is within the corporate network boundary. Don’t simply assume a correct password means the user must be who they say they are. Don’t conclude someone connecting from an unknown location must be on an exotic vacation.
Do harden the estate and prepare for a compromise as if it is inevitable. Do apply containment strategies and limit exposure if/when there is a breach of security by limiting what can be accessed, by whom, from where and from which device. Don’t allow access to unnecessary resources or provide excess privileges above what are needed. Audit access and monitor and alert on anomalous behaviour.
A walk in the park, right? Let’s break things down.
WHAT ARE THE PRINCIPLES OF ZERO TRUST SECURITY?
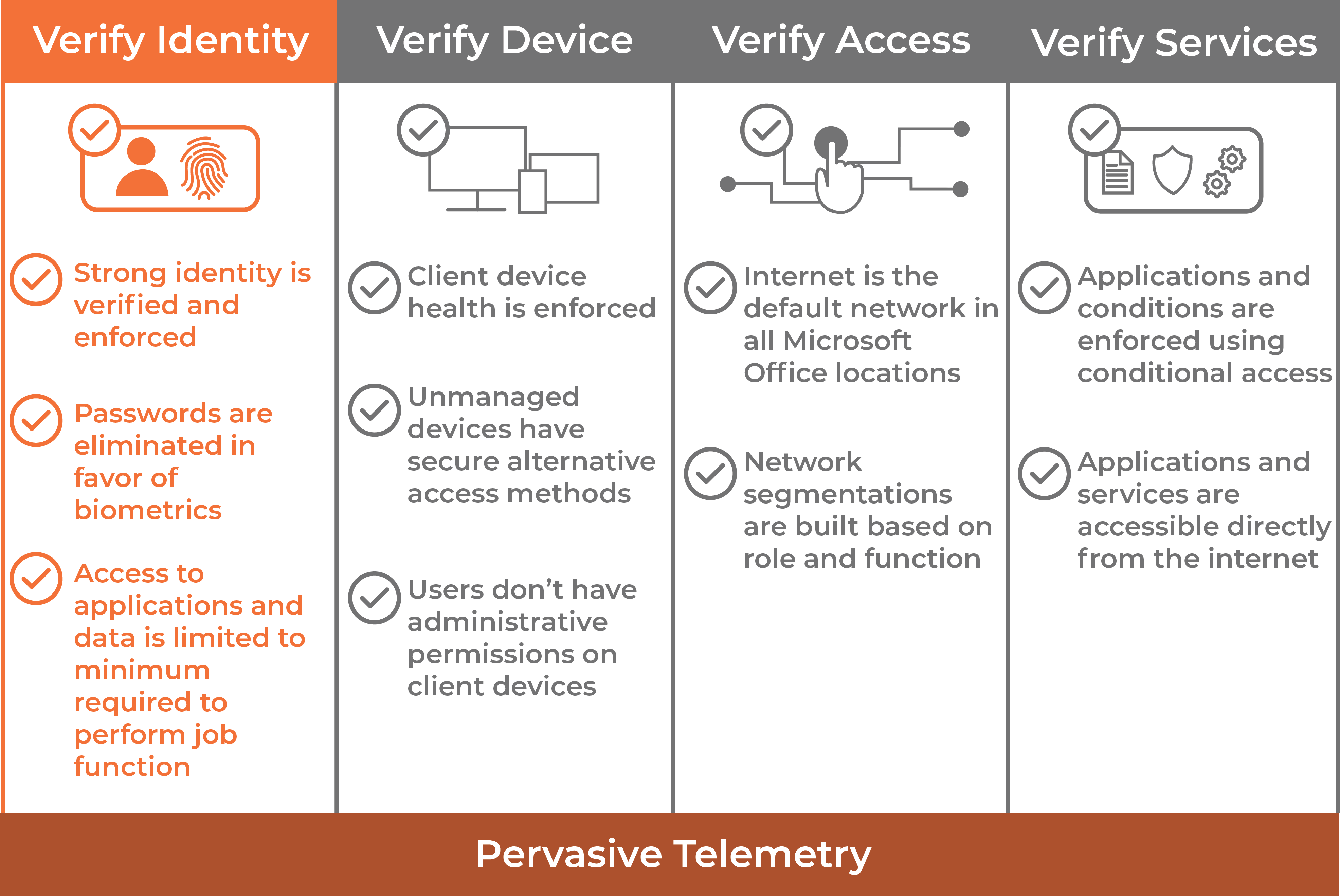
Never Trust, Always Verify (Verify Explicitly)
The first core principle of Zero Trust requires all touchpoints of an access request be scrutinised and forced to attest to their authenticity and level of trust. The manner of inspection can include the identity of the user, location the access is originating from, type of device used, security posture of the device, type of request, etc. With this approach, neither a compromised endpoint nor a stolen identity is enough to gain unauthorised access.
Only when all conditions of the request are satisfied will access be granted. This cycle is repeated for subsequent access requests and inherent trust is never implied.
Apply Least Privilege Access
Another core principle of Zero Trust is to provide just enough access to data and applications as is necessary to perform a function. In this way, we apply the principle of Assume Breach (see below) on a micro-scale. If we assume an identity will be compromised, limiting its level of access reduces the attack surface and potential impact of a breach.
Assume Breach
Another aspect of the principle of Zero Trust is to assume breach. This means the final core principle of Zero Trust is to assume a breach will occur rather than hoping the systems and data will always remain secure and protected. We must assume security controls will eventually be compromised (if they haven’t been already). This requires organisations to incorporate layers of security to minimise the impact of an attack when it does happen.
For example; segmenting networks to protect high-value server workloads from user networks where breaches are likely to occur. Only necessary traffic should be allowed between these network segments and it should be continuously monitored. Taken a step further, micro-segmentation (the concept of creating access policies between specific network interfaces on specific nodes within the individual segments) is gaining a lot of popularity as well.
WHAT ARE THE PILLARS OF ZERO TRUST ARCHITECTURE?
In this section, we will discuss the six (6) pillars of Zero Trust where controls and technologies should be implemented, including examples of relevant Microsoft products which address the specific pillar.
Identity
Zero Trust Identity requires verification of people, service accounts and devices through strong authentication and access compliance. Taken a step further, leveraging a single identity store as the ultimate source of truth prevents “identity sprawl” which happens when separate sets of credentials are maintained in various SaaS-based applications. Identity sprawl not only creates management headaches but also poses significant risk since it equates to multiple sets of vulnerable credentials per user.
Microsoft Azure Active Directory Single Sign-On (SSO) offers a robust solution to manage a single identity for all SaaS applications, monitored and protected by intelligent security telemetry with visibility and control.
Finally, a well thought out Role-Based Access Control (RBAC) strategy aligned to a least privilege approach is the mechanism used to define what level of access identities have across the other pillars.
More on Zero Trust Identity can be found in this video.
Endpoints (Devices)
Zero Trust Device Management (ZTDM) requires the ability to monitor, control and validate the level of trust of all devices in the organisation. This includes the ability to confirm the device meets a minimum set of standardised requirements which attest to its overall security posture and trustworthiness. ZTDM extends to user workstations, physical and virtual appliances and IoT devices.
Microsoft Endpoint Manager (Intune) offers a comprehensive cloud-first platform to manage endpoints including the ability to set Compliance Policies which will flag a device not aligned with a desired baseline.
Any device allowed to gain access to corporate resources must be considered within this pillar.
More on Zero Trust Endpoints can be found in this video.
Data
Zero Trust Data Security (ZTDS) requires data to be categorised and only accessible to those authorised following a least-privileged approach. Zero Trust Data Protection (ZTDP) requires data to be protected and encrypted both at rest and in transit.
Microsoft Purview, a unified data classification and governance solution contains several tools to support Data Security ranging from basic controls to highly complex content labelling including Data Loss Prevention (DLP), Information Protection, Message Encryption, Data Lifecycle Management, Compliance Management, Insider Risk Management and more.
All data created and owned by the organisation falls under this pillar. More on Zero Trust Data Security can be found in this video.
Applications
Zero Trust Application Access (ZTAA) requires applications to be correctly configured with appropriate controls and follow a least privilege access approach to both production as well as administration layers. Access to applications should be gated and available to only trusted users and devices and data movement into and out of the applications should be monitored.
Microsoft Defender for Cloud Apps offers a comprehensive set of controls to govern and monitor both Microsoft 365 and third-party SaaS applications in addition to fundamental controls like RBAC and Conditional Access policies. Unsanctioned applications can be prevented from running on endpoints with tools like AppLocker which can create whitelists of approved applications or Defender for Endpoint Indicators which can specifically block applications based flexible criteria.
All applications used by the organisation (both internal and cloud-based), must be considered under this pillar.
More on Zero Trust Application Access can be found in this video.
Infrastructure
Zero Trust Infrastructure (ZTI) requires an organisation to harden its on-premises and cloud infrastructure against attack. The management plan is often overlooked but is a critical aspect of a thorough Zero Trust Security program. In addition, limiting physical access to on-premises systems, patching for vulnerabilities and following a least privilege RBAC model are critical components of ZTI.
Tools such as Microsoft Defender for Cloud, Defender for Identity, Privileged Identity Management (PIM) and Conditional Access policies can aid in securing privileged access and monitoring.
All infrastructure components owned and managed by the organisation (both on-premises as well as cloud-based) must be considered within this pillar. More on Zero Trust Infrastructure can be found in this video.
Network
Zero Trust Network Access (ZTNA) requires the ability to segment network traffic appropriately based on a just-enough access approach. Additionally, monitoring and threat detection are commonly used to harden and protect at the network layer. Controlling access via adaptive policy and ensuring end-end encryption of all data are aspects of ZTNA.
There are some native Microsoft tools in Azure such as Just-in-Time Access, Azure Firewall, Network and Application Security Groups and Azure Bastion which can be leveraged in cloud-based or hybrid environments as well as a myriad of third-party tools. Microsoft Defender for Endpoint also contains protection mechanisms which can control network access at the endpoint (device) level.
All physical and virtual data networks with connectivity to the corporate environment, no matter how small, must be considered within this pillar.
More on Zero Trust Networks can be found in this video.
WHAT IMPACT WILL ZERO TRUST SECURITY HAVE ON USER EXPERIENCE?
By now you must be thinking this must be extremely disruptive to the poor end-users who will be challenged at every turn to prove themselves. This doesn’t have to be the case. In fact, if Zero Trust is introduced with a well thought out and carefully planned approach, it can complement the end-user experience.
Identity
Let’s take identity as an example. We all know Multifactor Authentication (MFA) must be at the heart of any organisation’s Zero Trust Security strategy. MFA is the process of requiring a user to present something they know (such as a password) and something they have (such as an identification device like a phone) to gain access.
While most users are accustomed to this already, it may be seen by some as burdensome to enter SMS codes to be granted access. To make this easier and more secure, most modern-day MFA products can leverage push notifications sent to authenticator applications running on smartphones and smartwatches which only require a tap to approve. Many of these applications can also be leveraged for MFA for many different sites and services in addition to the corporate assets.
For example, you can leverage the Microsoft Authenticator application on your smartphone for all kinds of MFA enrolments including one or more Microsoft 365 tenants, VPN connections, banking sites, benefits sites, password vaults and more. It can make your life easier since you can enrol all these different services into one convenient application to protect both your corporate as well as personal identities.
Endpoints
Let’s use identity as an example. We all know Multifactor Authentication (MFA) must. Next let’s look at device verification and attestation. What would it take to verify a device is compliant with an organisation’s security standards? The answer is simple – being managed.
Insentra helps clients leverage Intune to create a cloud-first modern management solution which allows organisations to control the security posture of the device, configure policies, VPN and Wi-Fi profiles, push software, manage updates and so on. Intune also reports the compliance status of a device based on a predetermined list of requirements such as having boot security enabled, being encrypted, having a firewall turned on, running up-to-date antimalware and Endpoint Detection and Response (EDR) products, etc. This compliance status can then be evaluated by Conditional Access policies to determine if the device should be granted access to corporate applications and data.
While this makes the business’s IT, Operations and Security teams happy by streamlining enrolments and mandating a security baseline, it also benefits the end users since they get to enjoy a modern device experience with an up-to-date operating system, automatically deployed software, single sign-on capability, consistent roaming data across devices and over-the-air provisioning of new devices which can be drop-shipped directly to their homes and remotely configured using Autopilot.
Taking these concepts a step further, let’s explore Windows Hello for Business. When users are required to register biometrics such as a fingerprint or facial recognition with Intune, this is considered and accepted as a form of MFA since the user must present something they have (finger or face) to access the device. Once they have authenticated to the device with something they have, they will no longer be challenged for MFA from any Microsoft 365 services or Azure Active Directory federated third-party SaaS applications.

Want to see a contented end-user? Let them sign into their laptop by simply looking at the webcam, thus granting them seamless access to all their line of business applications. They won’t even know this cutting-edge modern experience they are enjoying is also greatly enhancing the security posture of the organisation. It’s like pouring chocolate sauce on broccoli to have your kids eat a vegetable!
These transformational projects provide value for all stakeholders, including business leadership, those responsible for risk management, operations teams and end-users. This is a win-win experience for all – a fairly simple way to gain a strong foothold into the world of Zero Trust Security while enhancing the way devices are managed and delighting end-users with a truly modern platform and experience.
A Zero Trust Security implementation requires careful planning and execution to avoid disruptions to business. Everyone affected by incoming policy changes must be prepared and informed regarding what to expect and when. This level of planning and communication will help ensure a smooth transition to your Zero Trust model.
A bit more on Endpoint Management.
It should be noted Intune not only manages PCs but also MacOS and mobile devices such as iOS and Android. In addition to granular control of mobile devices when fully managed, Intune has a very well thought out and light-touch way of handling Bring Your Own Device (BYOD) scenarios to ensure corporate data is still secure even though the device itself may not be fully managed (given it is owned by the employee and not the business). The best part is all these device management capabilities are controlled under a single pane of glass!

WHAT IS THE COST IMPACT OF ZERO TRUST SECURITY?
The implementation of Zero Trust should not be looked at as a cost saving exercise for day-to-day operating costs. You should expect to have to purchase some products and services to support this model, though there may already be some foundational components available for use depending on what products are already owned by the organisation.
However, there is a cost savings conversation when discussing how Zero Trust Security can help in avoiding and/or mitigating the cost of data breaches. IBM’s “Cost of Data Breach Report 2021” found the cost of a breach averages $4.24 Million USD (which has increased 10% from the prior year). In this same report, IBM found a 42.3% decrease in cost of data breaches for organisations with a mature Zero Trust implementation as compared to organisations with no Zero Trust strategy in place.
Following the Assume Breach principle, organisations should not believe they will never be breached. In fact, the likelihood an organisation will never be breached is extremely low. The Forrester report “The 2021 State of Enterprise Breaches” found 63% of businesses have suffered a breach in the last 12 months (which is a 4% increase from the prior year).
These staggering numbers supports the notion whereby the cost for being prepared pales in comparison to the cost of incident response and clean-up which can include data recovery efforts, lost revenue during outages and, possibly the most destructive of all, the reputational impact.
To quote Benjamin Franklin, “By failing to prepare you are preparing to fail,” he also said: “An ounce of prevention is worth a pound of cure.” Mr. Franklin would have made a great cybersecurity consultant had he been born 300 years in the future!
Additional benefits which are more difficult to quantify with a Zero Trust Security implementation include:
- Standardising on comprehensive offerings such as Microsoft 365, Azure Active Directory and Defender often translate to consolidation and retirement of several (often legacy) disparate point solutions and services, each carrying management overhead and a Total Cost of Ownership (TCO)
- Reduced likelihood of regulatory violations and fines
- Modern compliance and cybersecurity guidelines typically align with a Zero Trust Strategy
- Diminished risk of data loss events and resulting legal costs
- Technology engagement has been shown to improve employee experience and satisfaction
- Increased business agility due to the flexibility and remote work capabilities inherent in a Zero Trust Security Model
- Faster adoption of new platform offerings aligned with a modern approach
HOW TO BEGIN YOUR ZERO TRUST SECURITY IMPLEMENTATION
OK. get ready for a bunch of tips here.
1
Start by taking an inventory of identities across the business and develop identity lifecycle processes to streamline onboarding and offboarding. Clean up user metadata and leverage dynamic group membership to manage entitlements to prevent users who change departments from retaining access no longer needed. Make sure you follow modern password policy guidance.
2
Work towards an approach of just enough and just-in-time access. Do not provide more access than needed for each business role. Separate administrative accounts from productivity accounts and challenge everyone for MFA all the time. Do not treat corporate networks as trusted IP ranges because doing so opens a gaping hole in a Zero Trust model should a user identity be compromised while on an internal network.
3
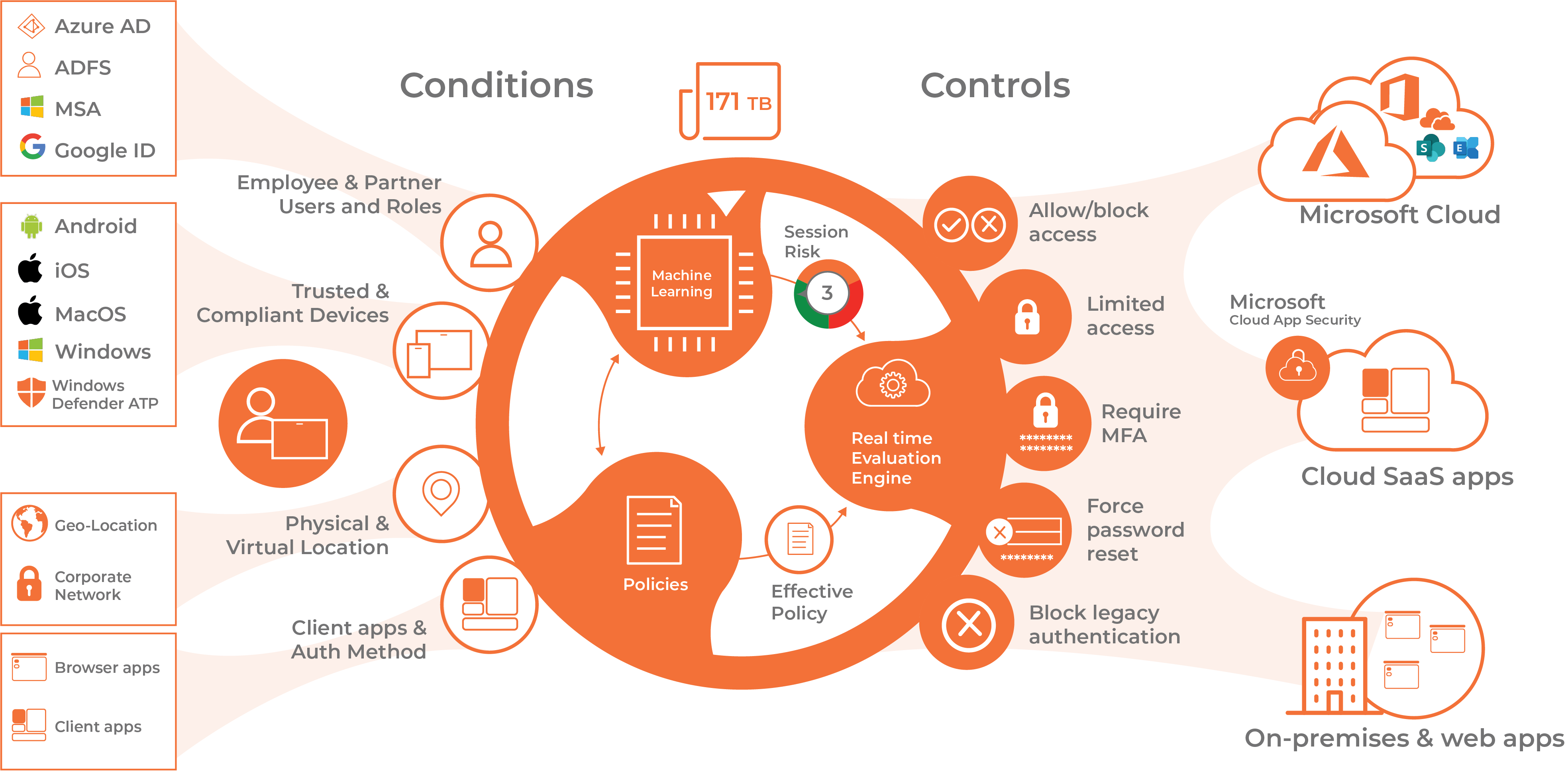
Leverage a robust and intelligent identity platform for accessing all Line-of-Business SaaS applications such as Azure Active Directory. Doing so allows you to grant and revoke access and entitlements from a single platform and provides a simplified approach to provisioning and de-provisioning, while combining security controls and signals across disparate systems into a single management platform with advanced threat detection capabilities.
4
Implement a modern device management strategy such as Microsoft Endpoint Manager (Intune) to gain full visibility and manageability of all devices permitted to access identities and data while ensuring they meet compliance requirements.
5
Segment workloads and monitor traffic within the network using the Zero Trust solutions offered by your favourite networking vendor (there are many powerful products, so it is valuable to research your options). Isolate the user networks, especially wireless, to limit access to sensitive workloads which serve no purpose and expose risk.
6
Develop an ‘Enterprise Access Model’ to separate admin accounts and Privilege Access Workstations (PAW) into tiers based on levels of sensitivity. Disallow higher-tiered privileged accounts from signing into lower-tiered devices and PAWs and vice-versa. Use separate admin accounts on-premises and in the cloud. Do not use shared local administrator credentials across endpoints. Instead, deploy a tool like Microsoft Local Administrator Password Service (LAPS) or, better yet, disable local admin accounts entirely!
7
Across all Microsoft cloud services, Conditional Access Policies (CAPs) are the glue holding it all together. As the name suggests, CAPs allow access to data and applications only when certain conditions are met. If those conditions are not met, access is not granted. This is the basis of Zero Trust and should be a fundamental part of any Microsoft 365 or Azure security posture. If you own Azure Active Directory Premium 1 or 2 and you are not using Conditional Access policies, then you should start today. Review Common Conditional Access policies to start. If you do not own Azure Active Directory Premium 1 or 2, leverage Conditional Access Security Defaults.
8
Develop contingency plans in the event of breach such as validating backup and recovery processes, communication policies (who, what, when and how) and risk assessments to determine mitigation strategies.
9
Lastly (and arguably the number one or two in terms of importance!) provide education to users on safe computing practices and why security controls are important for both corporate and personal identities. Ensure the education is continuous to keep security front of mind for all workers.
HOW TO DEVELOP A LONG TERM ZERO TRUST SECURITY STRATEGY ROADMAP IN THE MICROSOFT ECOSYSTEM
Rome wasn’t built in a day and a Zero Trust implementation won’t be either. We recommend you start with the higher value initiatives mentioned above and then look to further enhance from the established baseline. For example, within the Microsoft ecosystem, there are more advanced features in the higher SKUs which can complement the initial rollout with little to no user impact. Once your organisation is ready to mature its model, a level-up of SKU will bring loads of new functionality and features, made easier given the way Microsoft bundle their products. Here are some of the current features and services available from Microsoft today with more being developed:
Identity Protection
Identity Protection takes the fundamental identity controls and layers intelligent security and real-time analytics to make informed decisions about whether an identity has been compromised.
Pillar: Identity
Defender For Identity
Defender for Identity is a product which runs inside of the on-premises Active Directory environment and monitors Domain Controllers for anomalous behaviour, common reconnaissance and attack techniques.
Pillar: Identity, Infrastructure
Defender For Office 365
Defender for Office 365 allows organisations to detect malicious links and attachments in emails and documents before users can get a chance to run them. It also includes Anti Phishing protection.
Pillar: Applications, Data
Defender For Endpoint
Defender for Endpoint is a multifaceted enterprise security platform. It includes several components which can greatly improve the security posture of endpoint devices including:
- Threat and Vulnerability Management to discover, prioritise and remediate misconfigurations and vulnerabilities
- Attack Surface Reduction to harden known exploitable weaknesses in Endpoint
- Next-Generation Protection to detect modern zero-day threats
- Endpoint Detection and Response (EDR) to add detection, automation and response to threats which have gotten past your defences
- Automated Investigation and remediation to automate investigation activities and reduce the volume of alerts
- Microsoft Threat Experts offers a managed service providing proactive threat hunting, insights and rapid response to threats
- Network controls with the ability to allow or disallow access to specific locations and websites
Microsoft Defender for Endpoint also integrates with Microsoft Defender for Office 365 to enable security analysts to go upstream to investigate the entry point of an attack. Through threat intelligence sharing, attacks can be contained and blocked.
Pillar: Endpoints (Devices), Applications, Data, Network
Privileged Identity Management
Privileged Identity Management (PIM) offers the ability to provide just-in-time administrative access to privileged accounts. The elevations are tied to a workflow which can do things like send alert notifications, require the requestor to state the nature and purpose of why they are asking for elevation and even require the elevation request to be approved by other individual(s) within the organisation. This will serve to provide accountability and additional checks for privileged access usage.
Pillar: Identity, Infrastructure, Applications
Access Reviews
Access Reviews allow organisations to bundle entitlements into packages which can be applied to individuals within an organisation or extended to guest accounts in a B2B scenario. This could include access to specific data and applications, Teams, SharePoint libraries, permission sets, etc. These access packages can then be configured for regularly scheduled reviews to ensure access to these entitlements is still warranted for the individual users.
Pillar: Identity, Infrastructure, Applications, Data
Azure Active Directory Password Protection
Azure Active Directory Password Protection runs on-premises and integrates with Active Directory to disallow weak passwords by leveraging Microsoft’s real-time banned password lists as well as a custom list created by the customer.
Pillar: Identity
Defender For Cloud Apps
Microsoft Defender for Cloud Apps is a cloud-native Cloud Access Security Broker (CASB) which supports various deployment modes such as log collection for the discovery of Shadow IT and a broker for access to third-party SaaS applications with either API connectors or reverse proxy. It provides rich visibility and control over data movement and sophisticated analytics to identify and combat cyber threats across all Microsoft and third-party cloud services.
In addition, Defender for Cloud Apps can work in tandem with Defender for Endpoint to report on application usage and block access to applications unsanctioned by the enterprise.
Pillar: Applications, Data
Passwordless
It has been a long-known truth our passwords are the weakest link in modern cyber security. Passwordless technologies are still evolving, however, there are a few steps you can take to begin this journey. One is leveraging Windows Hello for Business mentioned earlier in this article.
Pillar: Identity, Endpoints (Devices), Applications, Data
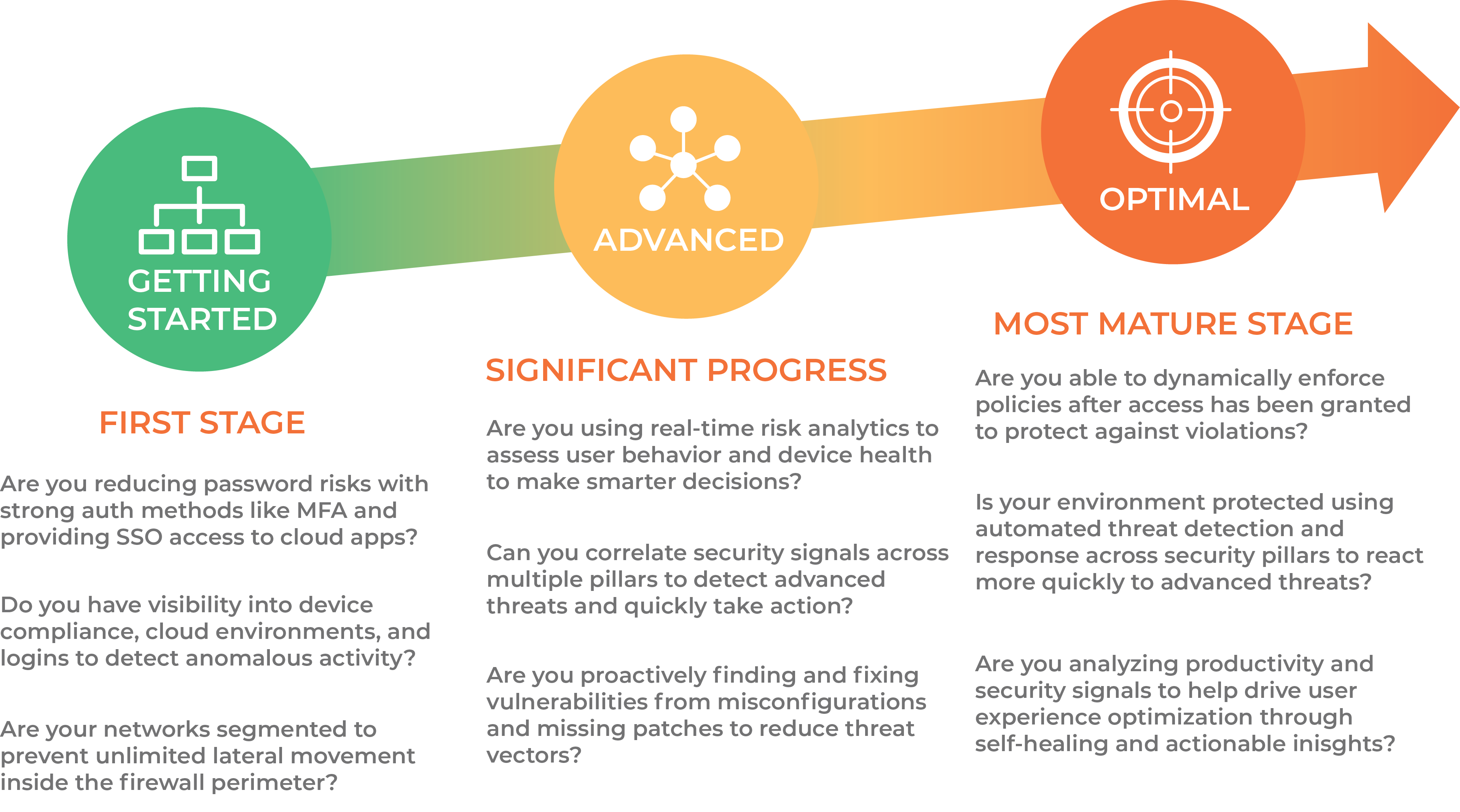
WHAT DOES A ZERO TRUST MATURITY MODEL LOOK LIKE?
Zero Trust Architecture
Zero Trust is not a destination, but an ongoing process which should be taken in bite sized chunks. It is good to stay closely connected to industry sources and trusted partners to stay informed and make sure you are doing your best to leverage current tools to protect your organisation (particularly if you already own some of these tools).
Every organisation’s journey will be different, yet you can use the following guide as a general blueprint for success. Answer these questions to see where you are in the process.
HOW INSENTRA CAN HELP WITH YOUR ZERO TRUST SECURITY STRATEGY
Looking to implement a Zero Trust Security strategy? Look no further than Insentra’s Zero Trust Assessment. Our team of expert architects and consultants have the knowledge and experience to ensure a successful rollout that won’t disrupt your day-to-day operations.
A poorly planned Zero Trust Security implementation can have catastrophic consequences for your business. That’s why choosing a trusted and strategic partner is critical. At Insentra, we offer highly customised solutions to meet the unique requirements of each customer. Our engagements range from specific tactical initiatives to long-term roadmap advisory consultations.
Whether you know exactly what you need and just want help planning, or you’re not sure where to start, we’re here to help. Trust us to guide you through every step of the process and ensure a successful outcome for your business. Contact us today for more information on how Insentra can help with your Zero Trust Security strategy.
DOWNLOAD THE ULTIMATE GUIDE
THANK YOU FOR YOUR SUBMISSION!






