One of the strengths of Symantec Endpoint Protection (SEP) has been the simplicity of the SEP client. Since Version 11, the SEP client has provided antivirus, firewall, intrusion prevention, application and device control, application whitelisting and more. This is an extremely effective combination of technologies that help to keep your endpoints secure.
When Symantec purchased Blue Coat they gained world class web proxy solutions. The Symantec Web Security Service (WSS) is a powerful tool to protect your endpoints from web-based threats. For roaming computers (not connected to the corporate network) WSS used the Unified Agent to connect computers to WSS. The Unified Agent is an excellent tool to enforce WSS policies. The challenge from a Symantec point of view is that it is another agent to manage on the endpoint. Wouldn’t it be great if there was a way to configure SEP to use WSS? There is, and this is how it works.
BACKGROUND
WSS has a number of Access Methods which can be used to get computers to connect to WSS. The key ones are:
- Firewall/VPN
- Unified Agent
- Explicit Proxy
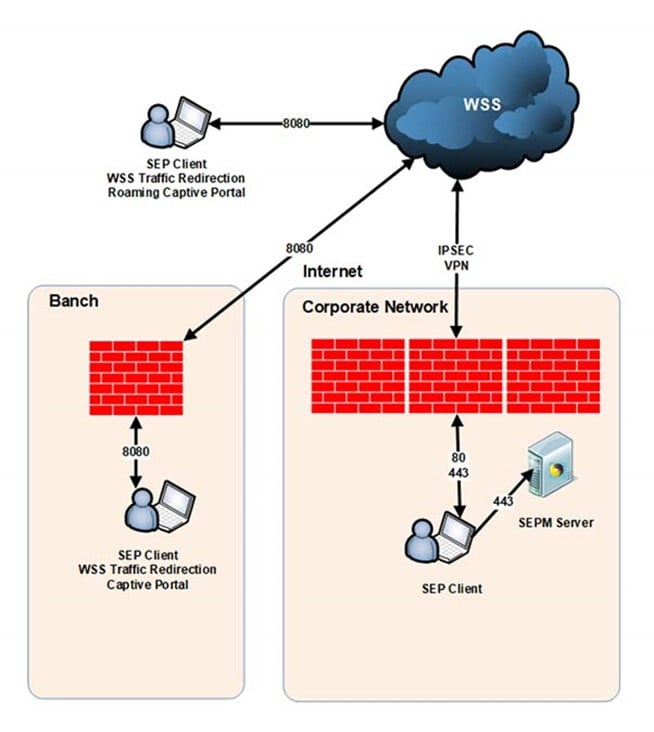
This solution uses the Firewall/VPN and Explicit Proxy access methods. For the Firewall/VPN access method, an IPSec VPN is set up between the corporate firewall and WSS. All web traffic from the corporate network is transparently directed to WSS through the IPSec tunnel.
The SEP clients not on the corporate network use the Explicit Proxy access method to direct all web traffic from the computers to WSS. The Explicit Proxy access method takes advantage of an auto-updating PAC file configured in the SEP client. So, this is a modified Explicit Proxy access method which is called SEP WSS Traffic Redirection. A Symantec Endpoint Protection Manager (SEPM) server is used to manage the SEP client.
The SEPM server is managed using the SEPM console. WSS is managed using the ThreatPulse portal using a web browser.
THE TECHNICAL STUFF
This section describes the technical aspects of this solution. It is not exhaustive in its coverage of the topic. The content assumes that the reader has at least some familiarity with WSS and SEP.
Note: The screenshots below are from a lab environment.
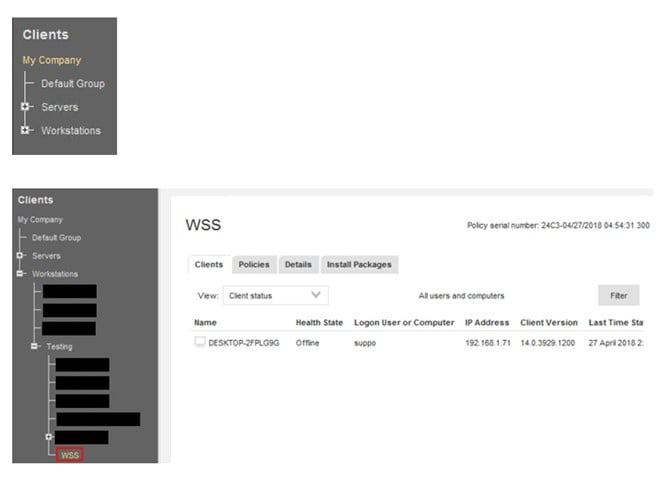
SEP Client Groups
Within the SEPM console, SEP clients are logically organised into Client Groups. For example, there can be server and/or workstation client groups. SEP policies are applied to Client Groups.
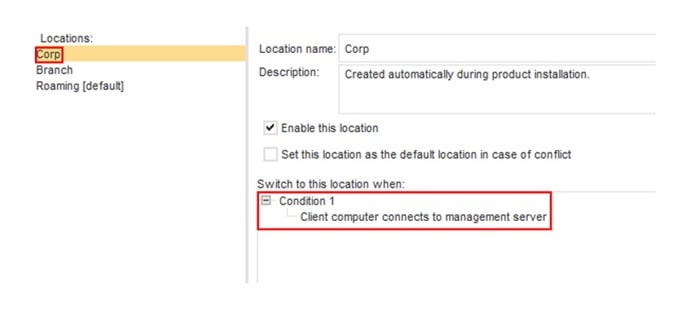
Auto-Location Switching
Auto-Location Switching can be used to further subdivide the SEP clients in a client group by criteria, such as the ability to connect to the SEP Management server or the SEP client’s DNS server, IP address, subnet, etc.
In this case there are three locations:
BRANCH
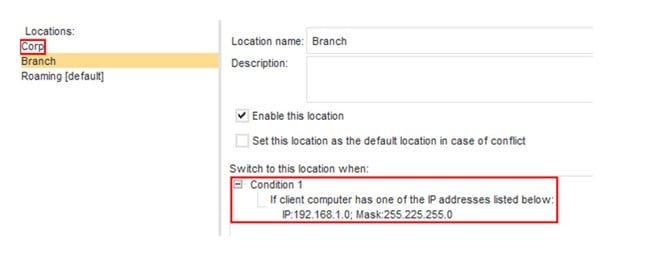
Note: You can add as many subnets as you have branch offices.
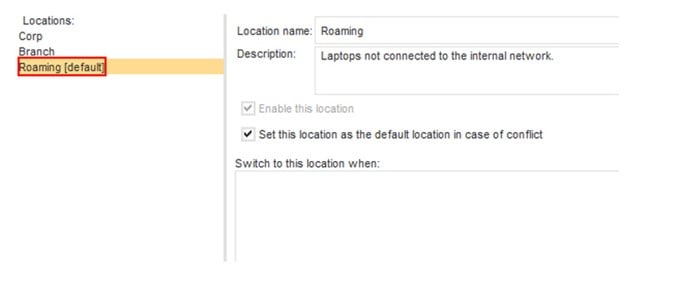
Note: This location matches all locations that are not evaluated in the Corp and Branch locations.
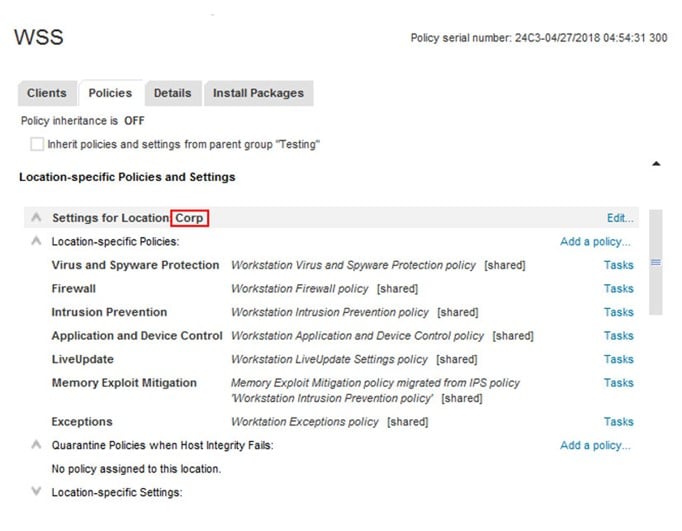
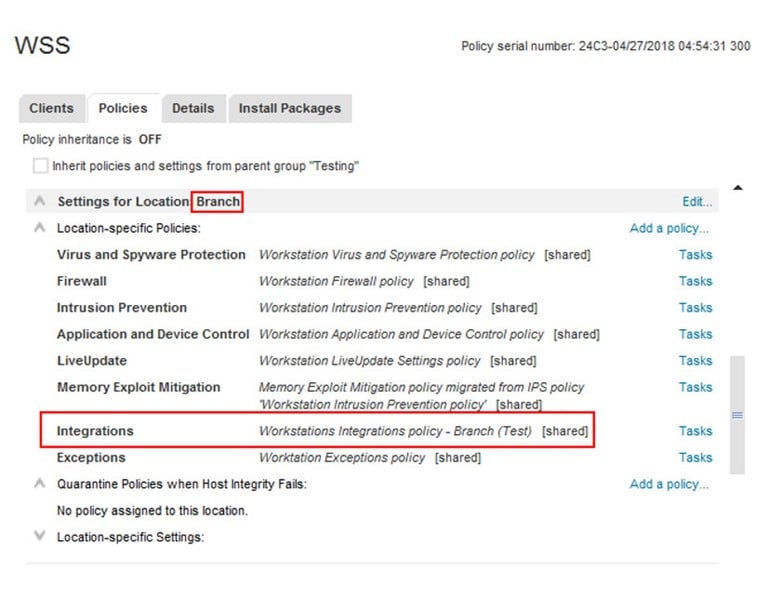
Locations
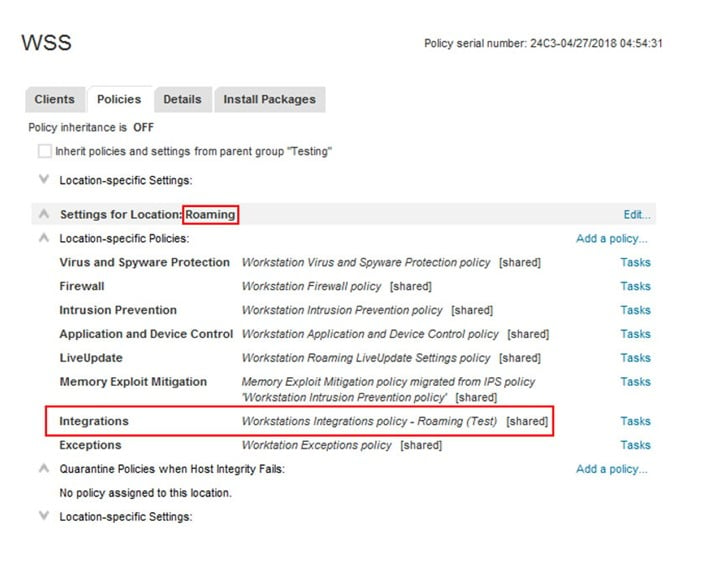
Each location has its own set of policies. The Integrations Policy is the SEP policy used to configure connectivity to WSS.
The Corp location has no Integrations Policy. Therefore, no PAC file will be set and all traffic will go through the firewall/VPN connection.
- Requirement 1: Location has to be created for the Corp site.
- Requirement 2: The firewall has to be configured to allow a Firewall/VPN connection to WSS.
- Option 1: Enable Captive Portal (A Firewall/VPN Authentication Policy has to be created for the Corp site).
CORP
BRANCH
The branch location uses the Workstations Integrations Policy – Branch policy.
- Requirement 1: A Location has to be added for each branch office in the WSS portal.
- Requirement 2: An Explicit Proxy Authentication Policy has to be created for each branch location. Captive Portal has to be enabled in WSS portal.
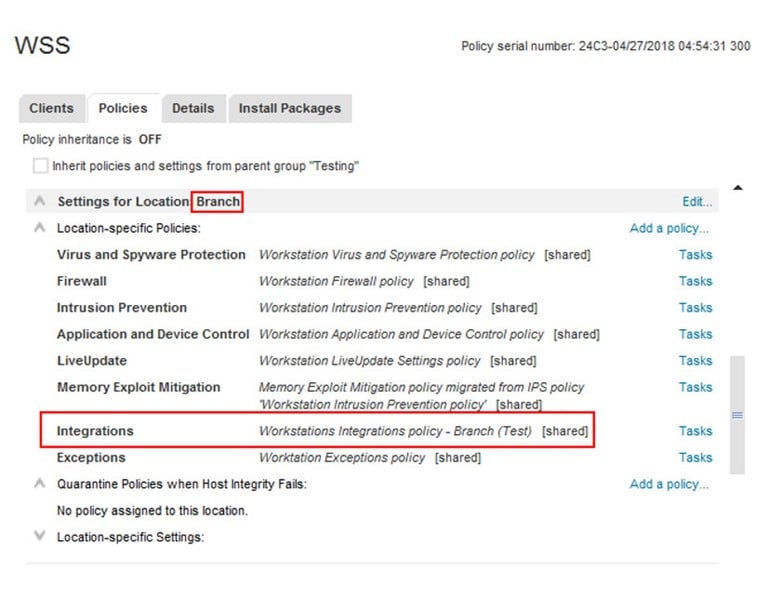
The Workstations Integrations Policy – Branch policy is configured to use https://portal.threatpulse.com/pac.
ROAMING
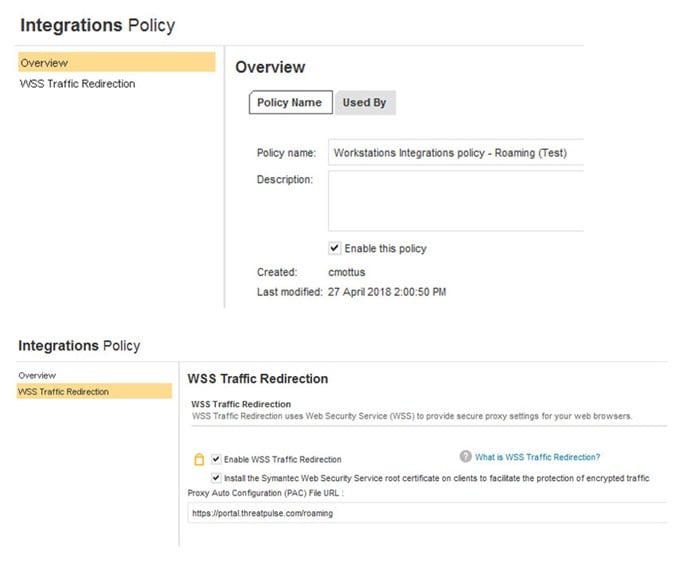
The Roaming location uses the Workstations Integrations Policy – Roaming policy.
- Requirement 1: Roaming Captive Portal has to be enabled in WSS portal.
The Workstations Integrations Policy – Roaming policy is configured to use https://portal.threatpulse.com/roaming.
How It All Works
If the user logs onto their computer and the computer is on the corporate network, the SEP client will be able to connect to the SEPM server. The SEP client will set automatically set the location to “Corp”. When the location is set to Corp there is no Integration policy applied and all web traffic will be directed to WSS by the Firewall/VPN connection.
If the user takes their computer to the branch office the SEP client will determine that the subnet that the computer is on is 192.168.1.0/24. The SEP client will automatically switch to the “Branch” location. When the user browses the Internet, their computer will configure their proxy settings based upon the PAC file downloaded from https://portal.threatpulse.com/pac. The user will have to authenticate using the Captive Portal using their domain credentials before they are allowed to browse the web.
If the user takes their computer home and the computer cannot find the SEPM server or the computer’s IP address is not on the 192.168.1.0/24 subnet, the location will automatically be switched to “Roaming”. When the user browses the Internet, their computer will configure their proxy settings based upon the PAC file downloaded from https://portal.threatpulse.com/roaming. The user will have to authenticate using the Roaming Captive Portal using their domain credentials before they are allowed to browse the web.
SUMMARY
This solution is an elegant way to extend Symantec Endpoint Protection’s already impressive capabilities. By integrating SEP with WSS, users will protected from web borne risks and the business will have positive control over which web content is available to users.










