Hey folks! Pure Awesomeness here and I know what you’re thinking… “where on earth have you been with your updates? We’ve been waiting impatiently for the next release!” Well, to tell you the truth, things have been absolute mayhem from trying to keep the kids entertained to working from home to finally sitting down and watching Season 5 of Money Heist. However, I’m back now with all of my energy focused on releasing a new kick a** blog.
For this blog, given the huge focus around all things security and combined with a recent deployment opportunity with a client, I’ve decided to share my wisdom and knowledge on the deployment of Microsoft Defender for Endpoint (let’s be honest, you probably already figured it out from the title of the blog, however, occasionally I like to build up the suspense).
Now before we kick things into gear, you know what you must do:
- Grab a cup of that world-famous Arabica infused liquid gold
- Watch my FastTrack Updates and don’t forget to Like/Share them because social media is now king
- Subscribe to Insentra on YouTube
Now buckle up and enjoy the ride as I take you through the wonder which is Microsoft Defender for Endpoint. Here we go!
WHAT IS DEFENDER FOR ENDPOINT?
Microsoft couldn’t just stop at Windows Defender. The wizards behind the scenes who have been responsible for building the Microsoft 365 cloud from the infant days of fog or mist to the cumulonimbus it is today (yep, I’m also a Nephrologist – had to refer to Google on this one), have introduced another portal into the ecosystem. With this portal, you can onboard your devices and it will provide you with a whole bunch of security threat detection insights and remediation tasks to apply. This is Pure Awesomeness’s definition. Microsoft’s definition goes like this – Microsoft Defender for Endpoint is an enterprise endpoint security platform designed to help enterprise networks prevent, detect, investigate and respond to advanced threats.
Pretty close if you ask me. Moving on!
So how do I onboard devices into the Defender portal (aka the new security.microsoft.com portal) I hear you ask? Keep reading my loyal apprentice for the answer to said question.
DEVICE ONBOARDING
Ok, so you have a fleet of Windows 10 devices (hopefully running 21H2…if not, email me separately and let’s talk) with Windows Defender preloaded and running as the active AV (of course it is right?). The business has procured M365 E5 licenses and now you want to take advantage of Microsoft Defender for Endpoint. Actually, let’s just call it MDE because let’s face it, we live by acronyms. How do you now onboard the devices? Well, you’ve got a few options available, depending on how you’re managing these Windows 10 devices today.
ConfigMgr
If you currently manage your Windows 10 fleet using ConfigMgr and have no intent to move management capabilities into Microsoft Endpoint Manager (or MEM because acronyms), firstly, contact me and let’s dive into why you don’t want to use MEM and then only if I’m convinced, you can proceed with step two, which is to create the Endpoint Protection policy directly through ConfigMgr and upload the MDE onboarding package. Don’t stress…I’m about to tell you how to get access to the onboarding package.
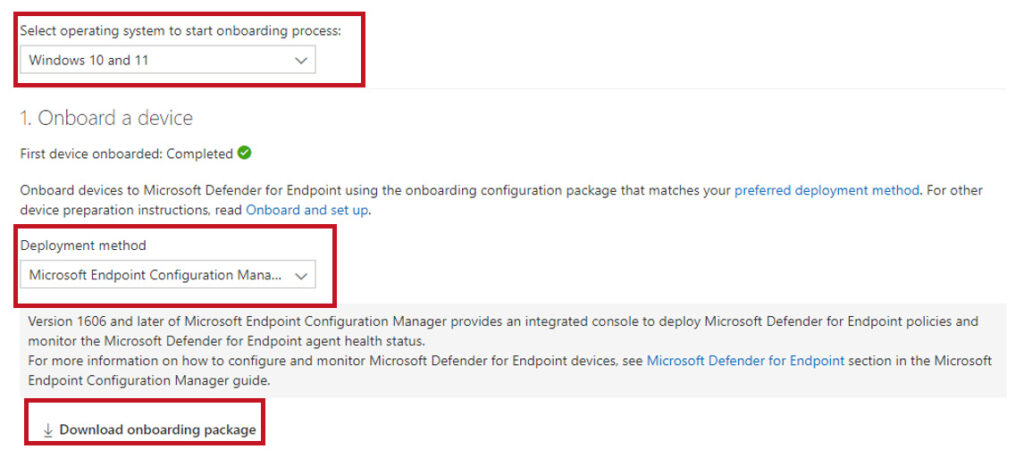
Log into the Defender Portal (security.microsoft.com) and then click on Settings – Endpoints – Onboarding Select Windows 10 as the operating system and select System Centre Configuration Manager or Microsoft Endpoint Configuration Manager (depending on the version of ConfigMgr you are running) as the deployment method and then click on download.
Next, in ConfigMgr, navigate to Asset and Compliance – Overview – Endpoint Protection – Microsoft Defender ATP Policies, create a new policy, upload the package file, assign it to your device collection and bingo…devices onboarded! Well not instantly, it’s the public cloud…since when is any change ever instant?
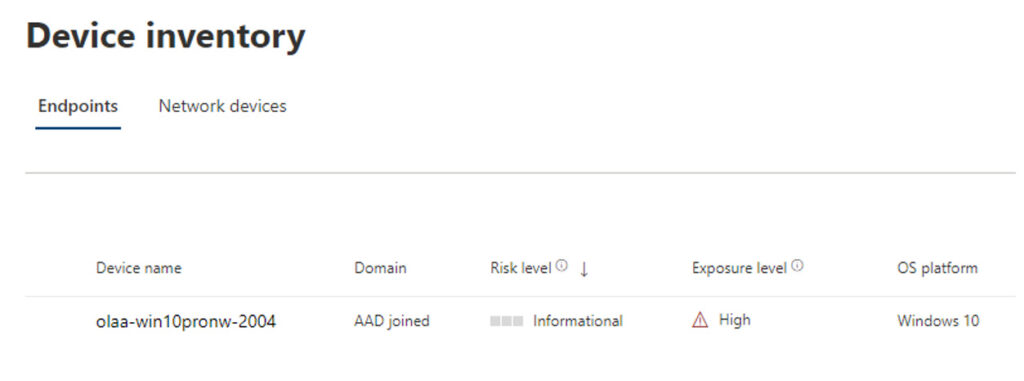
Then, log back into the Defender portal and under Device Inventory, you should see your onboarded devices!
I’d usually refer to the Carlton dance for a celebration like this but this time, it’s time for the Gru dance!
So, that’s onboarding through ConfigMgr. Next up, Intune!
INTUNE
OK, now I draw your attention to door number two, where your onboarding tasks are completed using Intune. The process is a little different than the ConfigMgr approach and requires the integration between Intune and Defender to be enabled as a prerequisite.
How does the integration get established you say? What kind of blog would this be if I didn’t tell you?
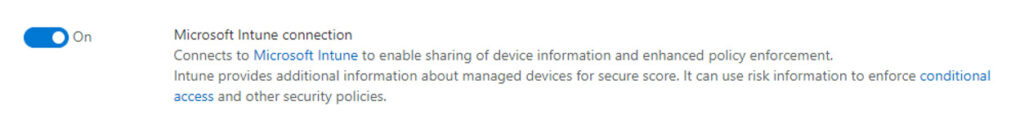
Log into the Defender portal and then click on Settings – Endpoints – Advanced Features. Scroll down until you see Microsoft Intune Connection and turn it on. It’s that simple!
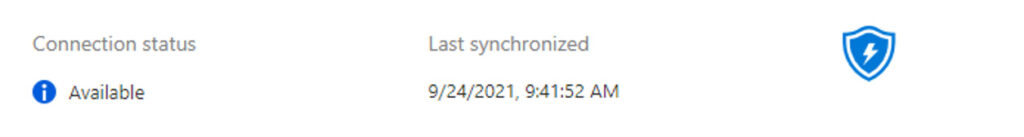
Once it’s turned on, log into the Intune portal and click Endpoint Security – Microsoft Defender for Endpoint and confirm the connection status shows Available. Once the connection is established, Intune and Defender will synchronise with each other at least once every 24 hours.
The one thing to note and this is where the onboarding process is different compared to ConfigMgr is once the integration is established between Intune and Defender, Intune receives an onboarding configuration package from MDE, so there’s nothing to download. However, you will need to configure a Configuration Profile for MDE to deploy the package to your Windows devices.
So, since this is a purely awesome blog written by Pure Awesomeness, I’m going to let you know how to configure the profile. To create the Configuration Profile, follow these steps:
- Click on Devices – Windows – Configuration Profiles
- Click Create Profile and select the following:
- Platform: Windows 10 and later
- Profile Type: Microsoft Defender for Endpoint (desktop devices running Windows 10 or later)
- Click Create
- Give the profile an easily identifiable name and click Next
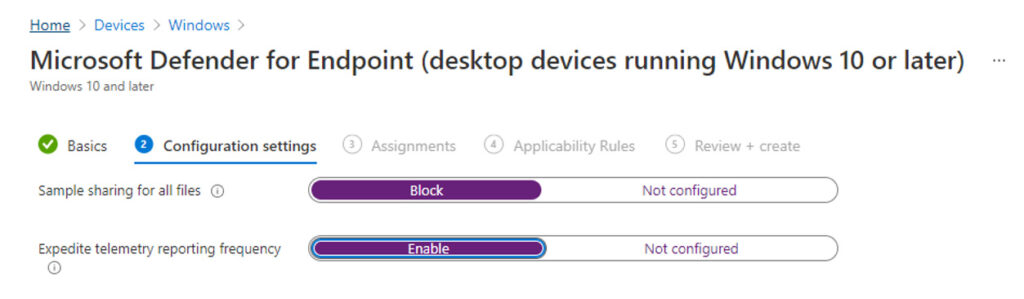
Configure the Endpoint Detection and Response (EDR) settings and click Next
- Assign the profile to a group of devices – start with a test/pilot group
- Set the Applicability Rules if need be
- Intune will only apply the profile to devices which meet the combined criteria of these rules
- Review the profile settings and click Create
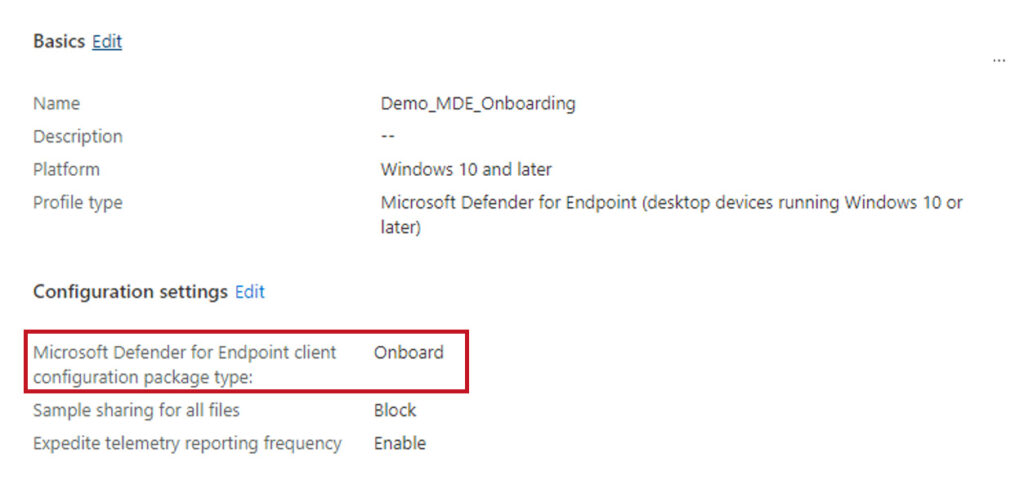
Once the profile has been created, you can check the properties to confirm the package type:
DETECTION TEST
Finally, once your devices are onboarded, how do you know they’ve been onboarded successfully? Well, Microsoft has kindly provided a detection script which can be run from each onboarded device. So, no more “I’ve onboarded my devices into MDE and given nothing is instant with the public cloud, I need to wait 8 hours for the devices to show up”.
Simply log into the devices you just onboarded and follow the below steps:
- Create a folder: C:test-MDATP-test
- Open an elevated command-line prompt on the device and run the below script:
- powershell.exe -NoExit -ExecutionPolicy Bypass -WindowStyle Hidden $ErrorActionPreference = ‘silentlycontinue’;(New-Object System.Net.WebClient).DownloadFile(‘http://127.0.0.1/1.exe’, ‘C:\test-MDATP-test\invoice.exe’);Start-Process ‘C:\test-MDATP-test\invoice.exe’
The command prompt window will close automatically. If successful, the detection test will be marked as completed and a new alert will appear in the portal for the onboarded device in about 10 minutes.
There you have it, folks! A brand new blog by yours truly on a topic I’ve started to dive into more. Stay tuned for additional releases on the beast which is MDE.
Until next time, Pure Awesomeness signing off!
“Many of life’s failures are people who did not realise how close they were to success when they gave up” – Thomas A. Edison










