So, finally I have decided to come out of retirement from writing blogs to help save humanity from the chaos around endpoint protection. In this blog I talk about the best cloud powered security solution available in the market, none other than the invincible Microsoft Defender for Endpoint formerly known as MDATP.
Why Should I Know About Microsoft Defender for Endpoint?
Microsoft Defender for Endpoint uses a combination of different technologies embedded into Windows 10 and Microsoft’s cloud services.
- Endpoint behavioural sensors: Built into Win 10, these sensors collect and process behavioural signals from the OS and forward the data collected by the sensor to the specific cloud instance of Microsoft Defender for Endpoint in your tenant.
- Cloud Security Analytics: This analytics engine uses a set of different technologies such as Big Data, Machine Learning and data from Microsoft 365 product suite and other online assets. Behavioural signals are then translated into detections, insights and recommended remediation to the detected threats.
- Threat Intelligence: This empowers Microsoft Defender for Endpoint to identify tools used by attackers, techniques and procedures and trigger alerts when the patterns match to the data collected by the sensor.
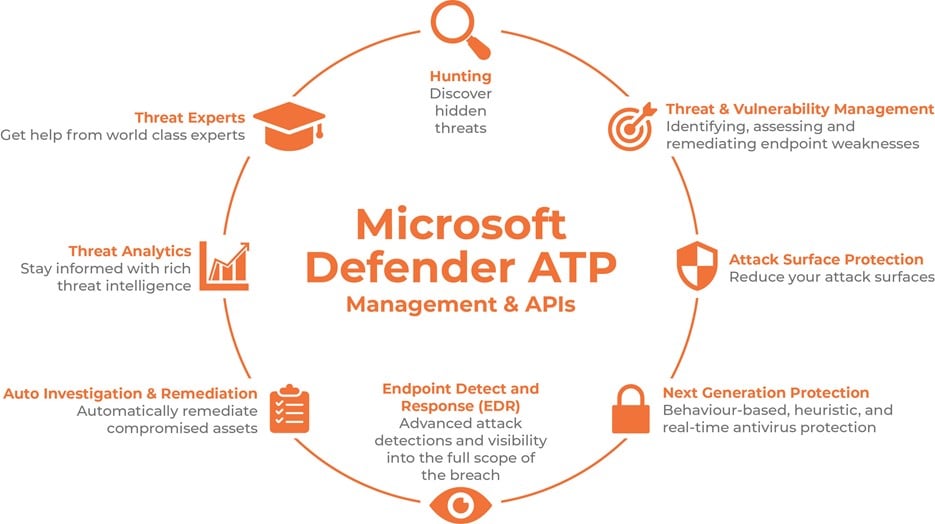
Microsoft Defender for Endpoint leverages all the above to provide a range of capabilities such as:
- Threat and Vulnerability Management: This is a risk-based approach to the discovery, prioritisation and remediation of the misconfigurations and vulnerabilities from an endpoint standpoint
- Attack Surface Reduction: This is the first line of defence for not exposing your territorial infrastructure to the bad guys. Admins can set up rules to reduce the attack surface area, perform Hardware based isolation, application control etc to strengthen the overall security
- Next Gen Protection: To catch all types of emerging threats Microsoft Defender for Endpoint uses next generation protection; aka Microsoft Defender Antivirus, to safeguard the security aspect of your network including zero-day threats
- Endpoint Detection and Response:
- Automated investigation and remediation (AIR): When fighting bad guys and their malicious intent, time is a critical factor. AIR needs to be turned on in the Microsoft Defender Security Centre. This reduces the amount of time and effort SecOps spend to remediate threats
- Secure Score: Secure Score for Microsoft Defender for Endpoint is a comprehensive report card of the state of the devices and the enterprise network which need to be protected. This gives us an understanding of how resilient the device and your network is to a threat. Like Secure Score for the overall tenant, it also provides recommendations to better your score
- Microsoft Threat Experts: This is proactive threat hunting intelligence built into Microsoft Defender for Endpoint which then empowers the SOC to be more efficient at their roles
- Integration with Microsoft Solutions: Microsoft Defender for Endpoint can be integrated with solutions such as Intune, Microsoft 365 ATP, Azure ATP, MCAS, Azure Security Centre etc
- Centralised configuration and management with API integration allowing you to automate workflows and integrate apps with the help of investigation and response APIs
While you digest the above information and integrate them into your mental faculties, I will enter into an alpha state of consciousness to figure out ways to best share how security enthusiasts can have a love affair with Microsoft Defender for Endpoint – All Strings Attached in my next blog.










