Many organisations choose to retire their existing 3rd party mail filtering service when they move to Exchange Online in Office 365 in favour for Microsoft’s native mail filtering service Exchange Online Protection (EOP). The benefits of doing so are numerous such as:
- removing complexity and unnecessary points of failure in your organisation’s mail flow
- reducing cost and simplifying billing, and
- subscribing to a world class mail filtering service managed by Microsoft itself.
Out-of-the-box, Exchange Online Protection is a great solution. Let’s look at ways we can fine tune it in the Exchange Admin Centre to perform better.
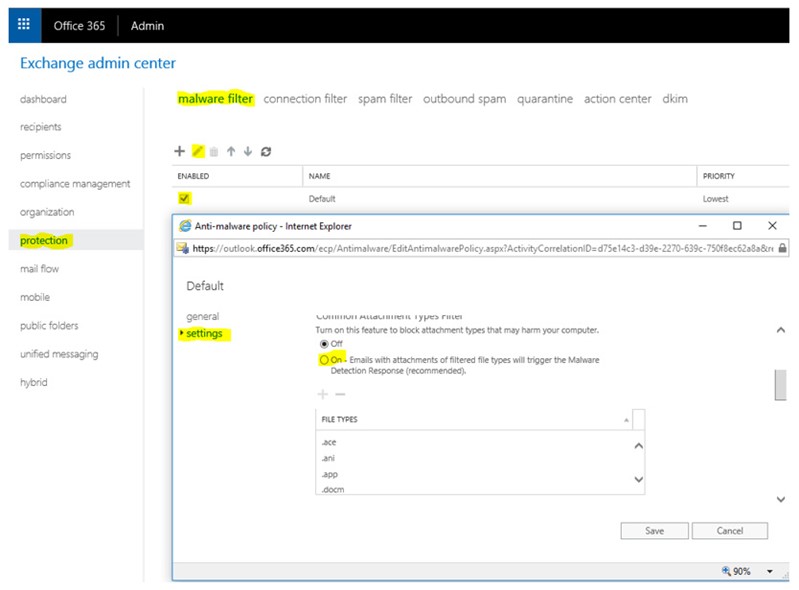
1. ENABLE “COMMON ATTACHMENT TYPES FILTER”
This filter triggers the Malware Detection Response which looks for mail flagged as malicious (quarantine, alert etc) for blacklisted email attachments such as .exe, .bat and .vbs . Disabled by default, you can enable this recommended feature under Protection Malware Filter by selecting the applied Malware filter policy and toggling the setting to On.
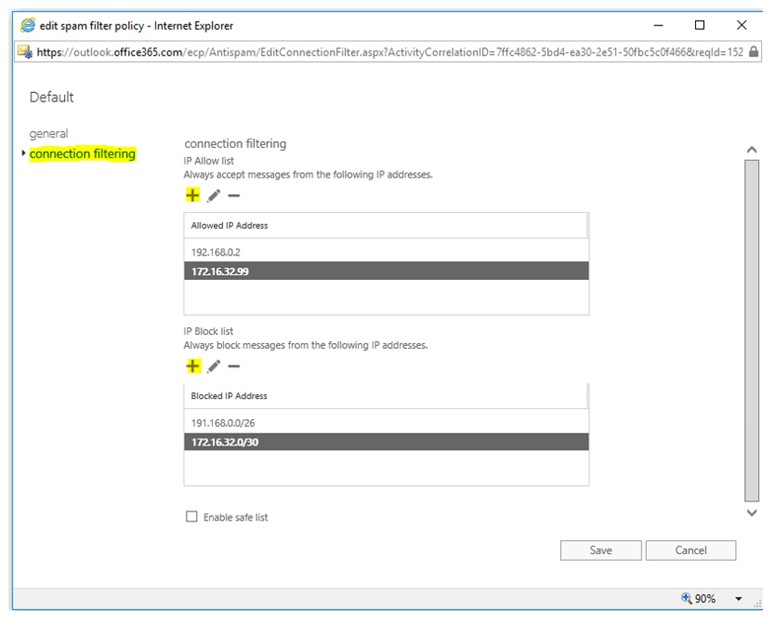
2. CONFIGURING IP ALLOW/BLOCK LIST
An IP Block list is a list of IP addresses that will always be rejected from sending email to your organisations. Conversely an IP whitelist is the opposite, ensuring emails originating from the IP addresses are delivered successfully. Adding to the Block List is often an iterative process whereby the admin learns of IP addresses over time and fine tunes the block list by adding these in as they are discovered. This feature, if used, should be reviewed over time to ensure that IP addresses haven’t been added in erroneously and considering that IP address shift and are reassigned over time. There is also the option here to block entire IP subnets and include IP addresses/subnets into an IP Allow list.
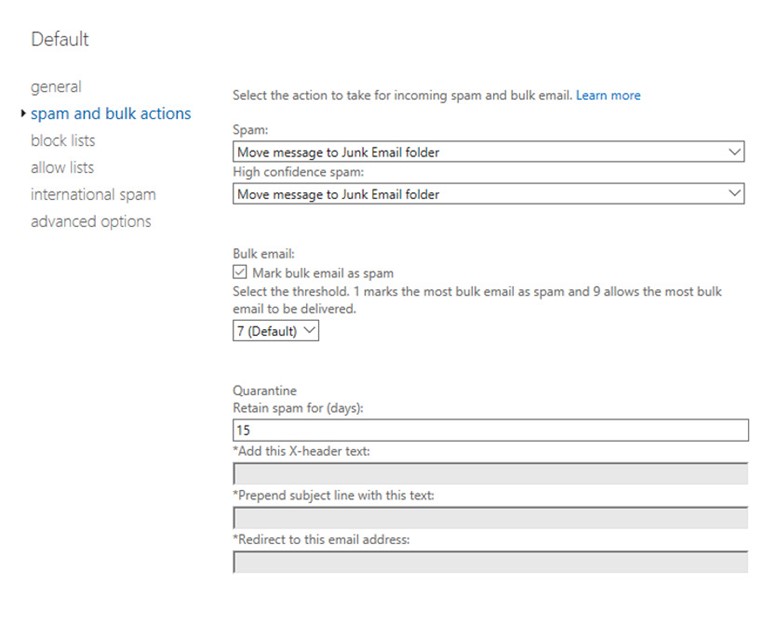
3. CONFIGURE SPAM AND BULK ACTIONS
This is where the bulk of configurable items for all your Spam filtering in Exchange Online can be found. You can configure the actions that will apply to mail marked as Spam;
- Move message to Junk Email folder
- Add X-Header, Prepend subject line with text
- Redirect message to email address
- Delete Message
- Quarantine Message
By default, mail marked as Spam will be delivered to the recipient but placed in the end users Junk Email folder, which may not be ideal as your admin will have no ability to prevent potentially malicious emails from being delivered to the end user. You may want to change this behaviour so that potentially malicious emails are Quarantined. You can also change the minimum bulk email Spam Confidence Level (SCL) value from the default of 7 to a higher value (potentially let’s through more bulk mail but results in less false positives) or a lower value (captures more unwanted bulk mail but may also mark more legitimate email as spam) and set the number of days spam is retained in Quarantine – the default being 15.
You may also want to take a more passive approach to spam handling. In this case you will find options to simply add text to the subject line such as “POTENTIAL SPAM” but deliver the mail to the inbox anyway, configure the option to redirect the potential spam to a different recipient such as an admin for human-eye-vetting or an alternative recipient e.g. spam@companyx.com for later review.
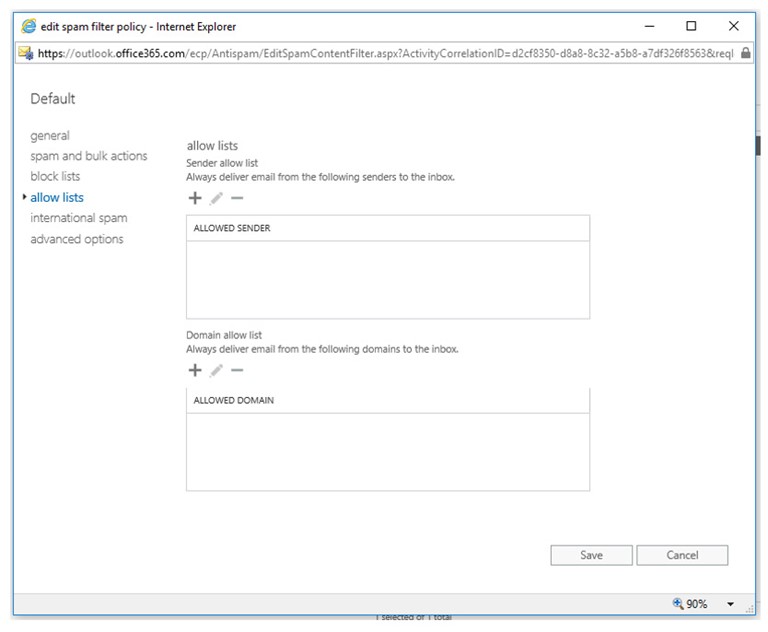
4. CONFIGURE EMAIL DOMAIN BLOCK AND ALLOW LISTS
The block and allow lists target specific email domains and/or users within those domains to prevent or allow them from emailing your organisation. It’s not usually advised to rely on this feature as email domains can often be spoofed. On top of this, the only way to bypass a domain/email block is to apply a transport rule above this policy to circumvent these rules, adding complexity to your solution. For this reason, IP allow/block lists are recommended over email/domain block and allow lists.
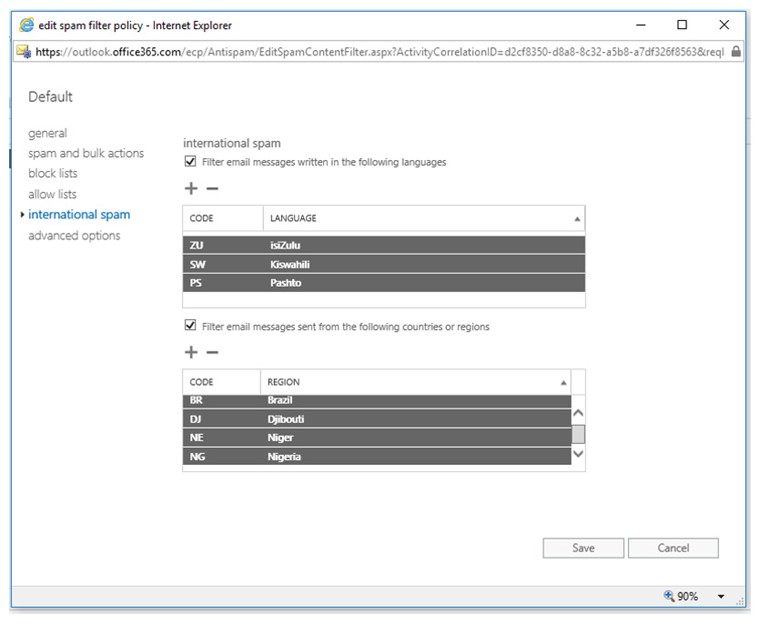
5. FILTER INTERNATIONAL SPAM
Entire countries and languages may belong to regions your organisation may never do business with and may only ever receive email from …oh…let’s say Nigeria for instance in the form of a spam (or a legitimate royal invitation). You can leverage the configure International Spam features to block emails based on the language used in the content of the email body or the specific country the email has originated from to further improve your spam filtering performance.
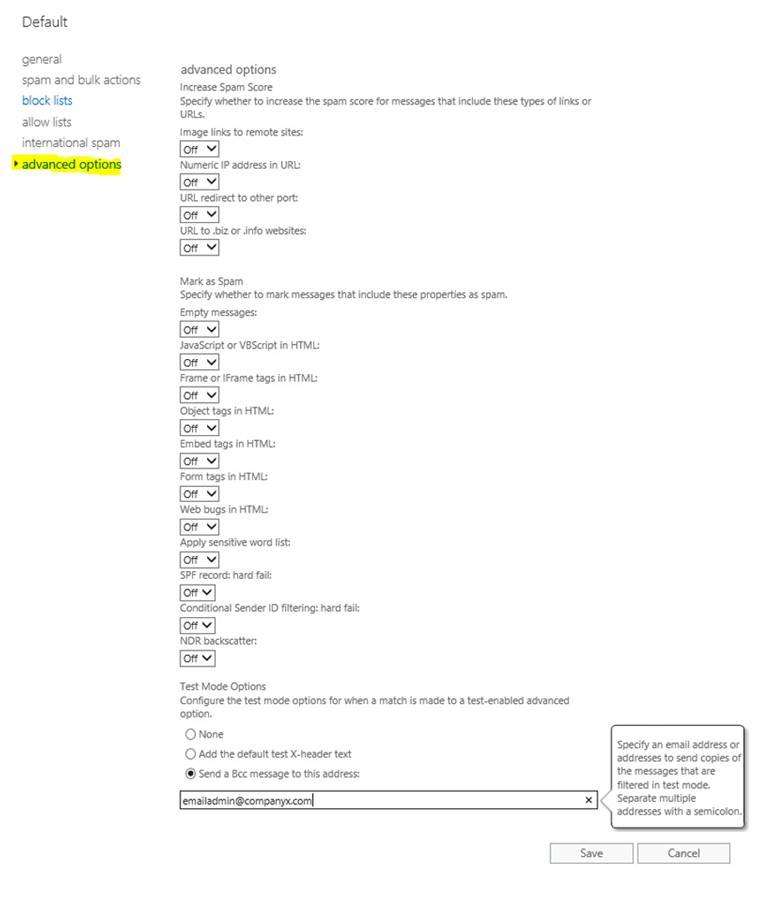
6. CONFIGURE ADVANCED OPTIONS
The Advanced Options of the spam filter policy can be a bit draconian in nature and all serve to either increase the SCL such as;
- Messages containing image links to remote sites
- Numeric IP addresses in hyperlinks
- URL redirects to a port other than 80 or 443 or biz/.info web domains
You can also take action to mark a message as spam based on whether the message contains an Empty Message, contain scripts in the content of the message and other configurable items. Of these, the SPF record: hard fail and Numeric IP address in URL are items worth considering enabling at a minimum. There is also an option to toggle on the Advanced Options in a test mode only so that admin’s can see the efficacy of these options first before actually applying spam actions to messages. For example; sending a copy of the suspected email to a recipient such as emailadmin@companyx.com.
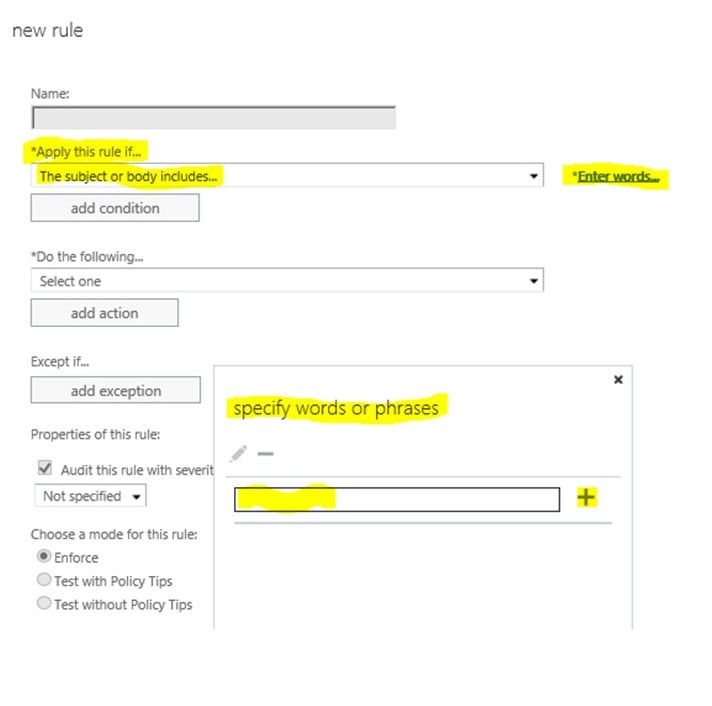
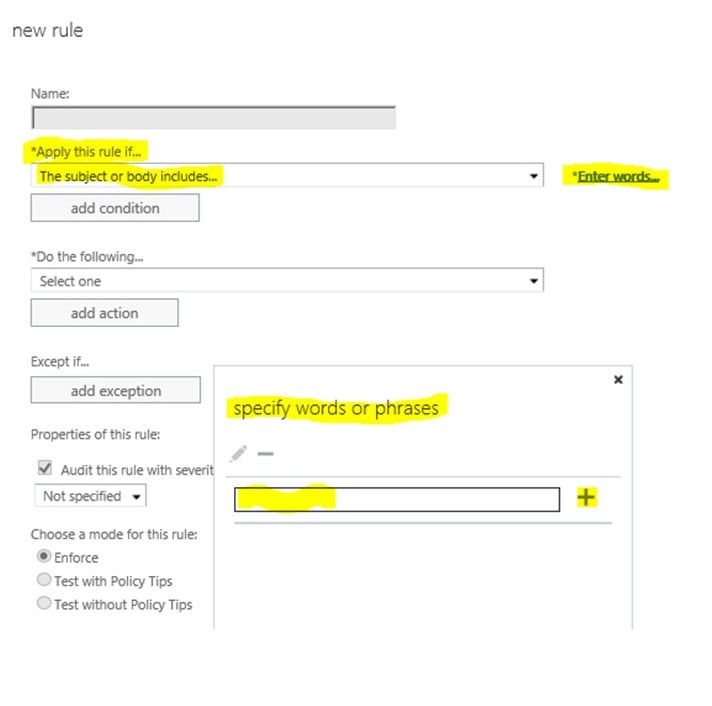
7. TRANSPORT RULES
The items above have covered all configurable options available to us for Exchange Online Protection, however it was always intended for mail filtering to be improved upon by leveraging Transport Rules in the Exchange Admin Center > Mail Flow section. It’s recommended to keep these at a minimum and to be very specific with the type of mail you target using transport rules to keep the complexity at a minimum but also because transport rules may take precedence over any other configuration you have in EOP.
The most common use of Transport Rules applied to mail filtering is for identifying and actioning potential spam based on phrases or text patterns and this is done by selecting the + sign and Create a new Rule. Specify a name and *Apply this rule if… The subject or body matches these text patterns or includes any of these words. This feature is not dissimilar to the Sensitive word list available in EOP however the key difference being there is no control over the word list in the Sensitive word list that is prepopulated.
SUMMARY
Exchange Online Protection is a great service out of the box and we have looked at leveraging native configurable items to improve its performance. Each organisation has different requirements and is similarly targeted by different types of spam. Over time, a mail filtering configuration matures and can be improved from day zero by replicating the rules and configurations from an existing service. Mail security can be improved further by taking advantage of scanning email attachments/email links, advanced spoofing checks and anti-phishing features available in the add-on service Advanced Threat Protection in Office 365. In the next blog I will cover what can be done to minimize the likelihood of your organisations outgoing mail from being marked as Spam.










