A long-awaited Azure Active Directory feature has finally made it into public preview, giving you the ability assign Azure AD Roles to Azure AD Groups. Quite a few organisations I have worked with over the past few years have been asking when this will finally happen… well the time is upon us!
Generally, IT organisations prefer to assign rights and permissions via groups and not to individual user accounts. This practice is supported across most Microsoft 365 and Azure services with one major exception, Azure AD roles, which are how various limited administrative rights are delegated to select users.
In order to assign Azure AD roles before this preview, a manual entry must be made to add the role, such as Exchange Administrator, to an individual user account. Even if you are using Microsoft Privileged Identity Management (PIM), which is Microsoft’s premium Just-in-Time (JIT) identity platform, you were still limited to assigning the eligible roles to users and not groups.
There are some limitations in the preview, such as the group must be a newly created cloud-based group and you must select the option to allow for this type of assignment as shown here:
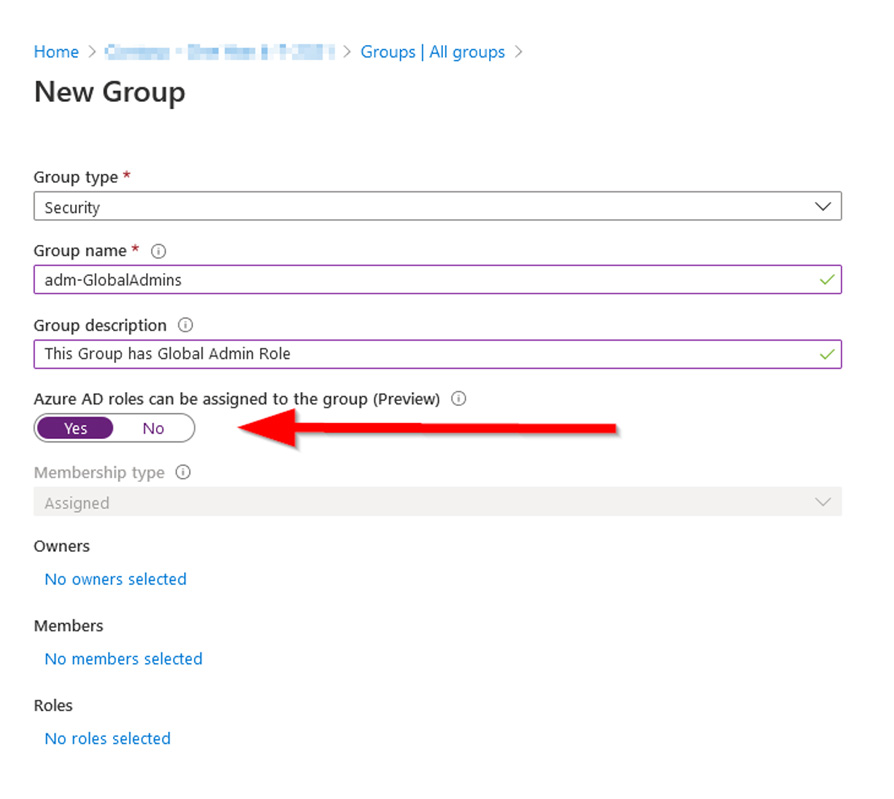
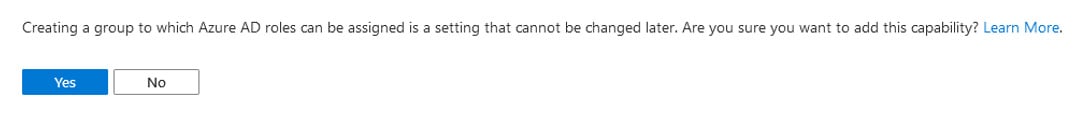
Notice that the Membership type gets grayed out if you choose ‘yes’ to this preview option, so these cannot be dynamic groups. When you click ‘Create’ you are met with this warning confirmation:
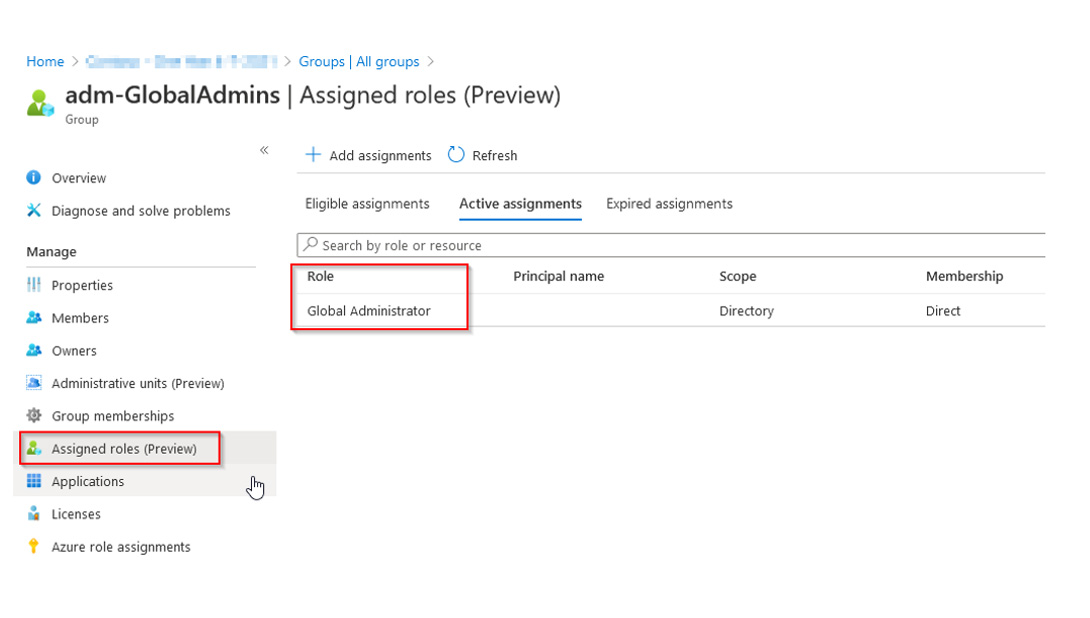
Once you create the group with this option enabled, you will be able to add it to an Azure AD role either from the ‘Group properties’ or from the ‘Azure AD Roles and administrators’ blade:
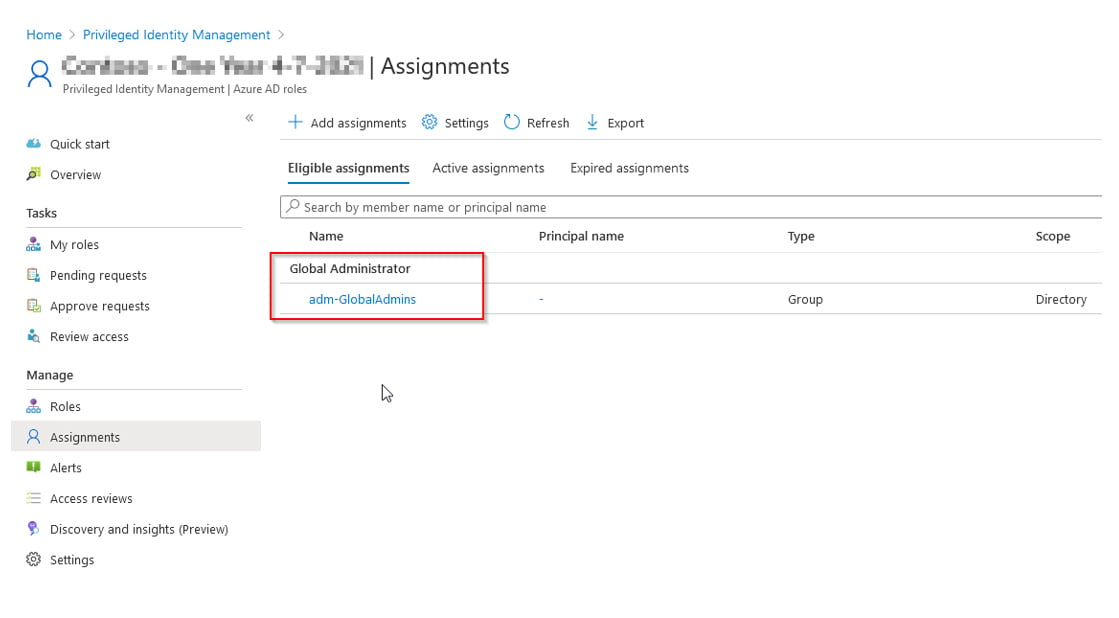
Or, from the PIM console to assign an eligible role to the group:
It should be known that one of the reasons why Microsoft has waited this long to enable this feature (I’ve been told by members of the Azure AD Product Group) is the risk which it poses. Microsoft has been cautious to allow this functionality due to the potential for organisations to inadvertently grant elevated permissions to inappropriate individuals. So, please do be careful with this feature. I would recommend using a special naming convention so these groups are easy to identify, such as adm-ExchangeAdmins or adm-GlobalAdmins.
Another limitation is these groups cannot be synced from on-premises Active Directory when Azure AD Connect is in use. This will be disappointing to some organisations who have been waiting specifically for the ability to delegate permissions in Azure AD based on AD group memberships. To those in which boat, hang tight, the announcement does state that this addition is on the roadmap. In the meantime, if you are really interested in bridging the gap in the short term, you may be able to get creative with some scripting to replicate group memberships, but I would only recommend this in an extreme case. Otherwise, I would just wait until the functionality has been added to the service.
As always, feel free to reach out if you have any questions or would like assistance planning out your Azure AD implementation.










