The endpoint strategy that sustained enterprises for decades is no longer fit for purpose. It was built for stable supply chains, predictable pricing, and orderly refresh cycles. Those conditions have shifted. What is emerging in their place is not a minor adjustment, but a fundamental reset.
Budget discussions were once routine. Hardware quotes arrived broadly in line with expectations, volume discounts were negotiated, devices were refreshed on schedule, and planning assumptions held. In 2026, that rhythm has fractured. Quotes are landing above forecast. Components that were plentiful a year ago are now constrained and repriced mid cycle. Finance leaders are questioning why endpoint expenditure is rising just as AI programmes demand capital and security teams request additional investment.
The difficult truth is that the long standing refresh model was designed for a market that no longer exists. Explaining that in a room where every line item is under scrutiny is challenging. Yet this is the reality enterprises now face. Not a temporary procurement disruption, but a structural reckoning with an endpoint strategy the market has outgrown.
The 3 forces that broke the model
The enterprise endpoint refresh cycle was built on a set of assumptions that held for decades. Hardware costs declined steadily. Component supply was abundant and globally optimised. Operating system lifecycles were long and predictable. Refreshing devices was as much a financial convenience as an operational one.
Three forces have now converged to invalidate each of those assumptions simultaneously.
Force 1: Memory and Component Scarcity Driven by AI Infrastructure Demand
The first is memory and component scarcity driven by AI infrastructure demand. With Samsung, SK Hynix, and Micron, which together produce the majority of global DRAM and NAND flash, have redirected their constrained cleanroom capacity toward high bandwidth memory used in AI accelerators. While discussion of the AI boom often centres on GPU availability and hyperscaler investment, far less attention is paid to the downstream supply chain effects at device level. NAND flash and memory constraints are forecast to tighten through 2026, with direct impacts on pricing and availability.¹ Memory prices rose by as much as 90 per cent in Q1 2026 compared with Q4 2025.² Lenovo, the world’s largest PC manufacturer, has already warned that shortages are affecting shipments and confirmed it has increased enterprise pricing to offset higher input costs.³ When a market leader adjusts pricing mid cycle, procurement assumptions set even a year earlier can quickly become unreliable.

Force 2: Tariff Volatility
Cross-border hardware supply chains spent the better part of a decade being treated as background infrastructure stable, optimised, and largely invisible to planning processes. That assumption has eroded. Gartner identified tariff volatility as a direct driver of enterprise refresh behaviour in 2026,⁴ and PC vendors have been explicit that they lack the margin to absorb the exposure. The cost passes through. And unlike memory pricing, tariff risk can move significantly in weeks rather than quarters, making it almost impossible to model in a multi-year capital plan.
Force 3: The Windows 10 End-of-Support Cliff
Microsoft ended support for Windows 10 on 14 October 2025. 5 For organisations that were not prepared, the choices narrowed quickly. They could fast track a hardware refresh into a component market already constrained and repriced, pay for Extended Security Updates which Gartner identified as an added and increasing cost, 4 or continue running unpatched devices and accept the security risk of operating outside vendor support. None of these options were cost effective. All drew from the same already pressured budgets.
The convergence of these forces led to a predictable outcome. The Windows 10 deadline concentrated upgrade demand just as AI driven infrastructure spend tightened supply and lifted prices. Budgets expanded, timelines compressed and security exceptions increased. The resulting endpoint estate became more expensive and less consistent, without delivering meaningful security gains. This dynamic now shapes enterprise endpoint strategy in 2026 and is unlikely to ease in the next budget cycle.
The damage you cannot see on the hardware invoice
Hardware inflation is the visible issue. The less visible and often more strategic impact is capital displacement. Global IT spending now exceeds six trillion dollars, with data centre and AI infrastructure taking a disproportionate and growing share.⁶ Technology leaders are not just managing a procurement challenge. They are navigating internal capital competition, where endpoint refresh spend competes directly with AI programmes, cloud investment and critical security capability.
Every additional dollar committed to device procurement is a dollar not available for AI initiatives, threat detection capability, incident response tooling, or the security talent required to operate both.
This trade off is rarely central in endpoint refresh discussions, yet it is being made in budget cycles now, often without clear visibility. In an environment where CISO budgets face the same pressure as every other technology line item, the opportunity cost is significant.
The operational impact compounds the financial strain. A forced refresh differs materially from a planned one. Compressed timelines drive inconsistent builds, driver conflicts and increased field support demand. Temporary security exceptions become embedded through inertia. The refresh intended to simplify the estate frequently leaves it more complex.
After the cost and disruption, the core security posture remains unchanged. A new Windows device still carries a distributed operating system that requires continual patching, reimaging and remediation. Replacing hardware does not reduce the attack surface or shift the security model. Teams continue operating reactively, at greater speed and cost, without structural improvement.
Shifting endpoint strategy from replacement to extension
The defining shift in enterprise endpoint strategy in 2026 is not vendor driven. It is driven by capital pressure, supply chain realignment and the recognition that a distributed, device centric model has always been operationally expensive. That cost was easier to ignore when hardware was cheap, supply was stable and security scrutiny was lower. Those conditions no longer apply.
Leading organisations are no longer measuring success by how quickly devices are replaced, but by how long they can be sustained without degrading security or experience. The focus has moved from concentrating capability at the edge to consolidating compute, storage and governance in the data centre and cloud, where scale delivers structural advantage.
This shift also reflects supply chain reality. AI investment has concentrated semiconductor capacity in centralised infrastructure, giving data centres and hyperscalers preferential access to constrained components. Moving processing closer to these environments is not just cost control. It aligns architecture with where long term infrastructure advantage is being built.
Repositioning the endpoint as a secure access layer rather than a primary compute platform is an architectural decision. Through VDI, DaaS and SaaS models, productivity is decoupled from the device. Endpoints become simpler, more interchangeable and less exposed, while governance, resilience and security are strengthened centrally.
What the shift looks like in practice
IGEL’s Adaptive Secure DesktopTM is a secure endpoint operating system designed for organisations shifting to SaaS, DaaS, VDI and secure browser environments. Built with lower resource requirements than traditional desktop operating systems,⁷ it reframes endpoint strategy across four areas.
1. Extend asset life without compromising security
Devices that cannot support a modern Windows environment can be repurposed as secure access endpoints rather than replaced. This defers refresh cycles and avoids over specification driven by operating system overhead. The result is lower capital expenditure and reduced exposure to volatile component pricing, without sacrificing user experience or security posture.
2. Reduce operational overhead
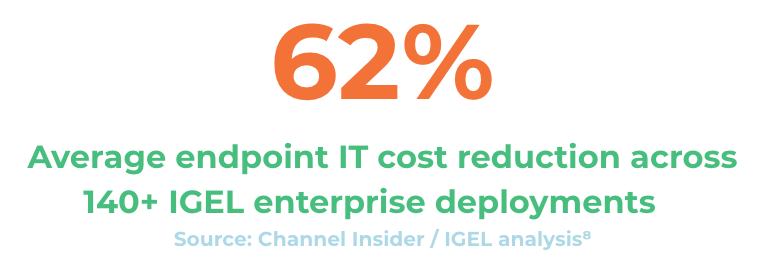
By minimising what runs locally, the operational surface shrinks. Provisioning accelerates, ticket volumes fall and patching and reimaging requirements reduce. In more than 140 enterprise deployments, IGEL reports average endpoint IT cost reductions of 62 percent, with savings exceeding 900,000 dollars annually per organisation.8 These figures are vendor reported and should be validated against comparable environments, but the mechanism is clear. Fewer moving parts create fewer failure modes and enable scale without proportional headcount growth.
3. Shift security posture structurally
Traditional endpoints are reactive by design, relying on detection and response after compromise. IGEL’s Preventative Security ModelTM removes common attack conditions at the endpoint layer. There is no persistent local file system for malware, no local credential store to harvest and no durable execution environment for persistence. Sessions restart from a clean state, reducing the attack surface structurally rather than incrementally.
4. Support hybrid environments
Most enterprises operate across SaaS, VDI, DaaS and legacy application models simultaneously. IGEL provides a single, standardised access layer across these environments, enabling consistent governance without parallel management frameworks. The transition can begin within the current estate and evolve over time, rather than requiring a complete architectural reset.
Rethinking the Endpoint for a Capital Constrained Era
The economics of the traditional endpoint refresh model no longer hold. Hardware inflation, supply chain concentration and operating system deadlines have exposed a strategy built for stability in a market defined by volatility. Continuing to accelerate replacement cycles in this environment increases capital pressure without delivering structural security or operational improvement.
The organisations that adapt will not focus on marginal savings in their next device order. They will challenge the assumption that productivity and security must remain anchored to high cost, complex endpoint hardware. By shifting from replacement cycles to extension cycles and repositioning the endpoint as a secure access layer, they release capital, simplify operations and strengthen security at the architectural level.
Endpoint strategy is no longer a procurement exercise. It is a capital allocation and risk management decision. Those who realign their architecture accordingly will gain compounding advantage in cost control, scalability and resilience.
If you would like to explore what this shift could look like in your environment, contact us to start the conversation.
References
¹ IDC Market Analysis, NAND flash and memory supply constraints forecast, 2026.
² Counterpoint Research, “Memory Prices Surge Up to 90% From Q4 2025,” 2026. counterpointresearch.com
³ Reuters, “China’s Lenovo warns of PC shipment pressure from memory shortage,” February 2026. reuters.com
⁴ Gartner, “Gartner Says Worldwide PC Shipments Increased 9.3% in Fourth Quarter of 2025,” January 2026. gartner.com
⁵ Microsoft Support, “Windows 10 support has ended on October 14, 2025.” support.microsoft.com
⁶ Deloitte, “2026 Global Hardware and Consumer Tech Industry Outlook.” deloitte.com
⁷ IGEL, “IGEL Catalyses a New Era of EUC Transformation and Trusted Endpoint Security.” igel.com
⁸ Channel Insider, “IGEL Finds Enterprises Are Cutting Endpoint IT Costs by 62%.” channelinsider.com