If we are to accept the now common statement “Information is your most valuable asset” then it is fair to say this information must be protected and have controlled access. Any risks associated with data loss, IP theft, sharing of information or compliance breaches should be fully understood, together with any potential financial or reputational damage resulting from a data loss or breach event.
Like all high value assets, control over who has access, and more importantly why, is critical. Failure to have controls in place, may limit the ability to recover from an event, and/or a be the reason for a failed information governance audit. If the information retained in your business is of high value, then naturally it becomes a target, the audit process is part of your protection strategy and undergoing, or worst case, failing an audit can be a daunting process
I understand, but tell me more about why I should care
Many businesses are audited every year and preparation for these audits often involves a mad scramble by IT departments to ensure they can prove the right people have access to the right information. Access reports are created, carved up and sent to managers, seeking confirmation the right people have access. This process works OK for the traditional file shares however, with data sharing made so simple with OneDrive, SharePoint and particularly Teams, who really knows who has access to what? Can you remember everyone who you have shared a file with?
Information governance audits can be the reputational make or break for a business. Being prepared for an audit or recovering from a failed audit and preparing for “Re-Audit” is critical and should not be underestimated. Costs to a business of a failed audit can spiral as teams within the organisation “rally” to resolve failed audit controls, often leading to the implementation of unnecessary tools or products. If you had the ability to quickly see who has access to what data and, importantly the reason why, audits can become a walk in the park.
I am in the “Re-Audit” category due to a recent “uncomfortable” experience and need to move to the Pre-Audit level of readiness
The image below portrays an all too familiar outcome for organisations in the “Re-Audit” category where some new audit areas are identified, or worst case, there are repeat control items highlighting potential gaps in ability to resolve items or incomplete actions.
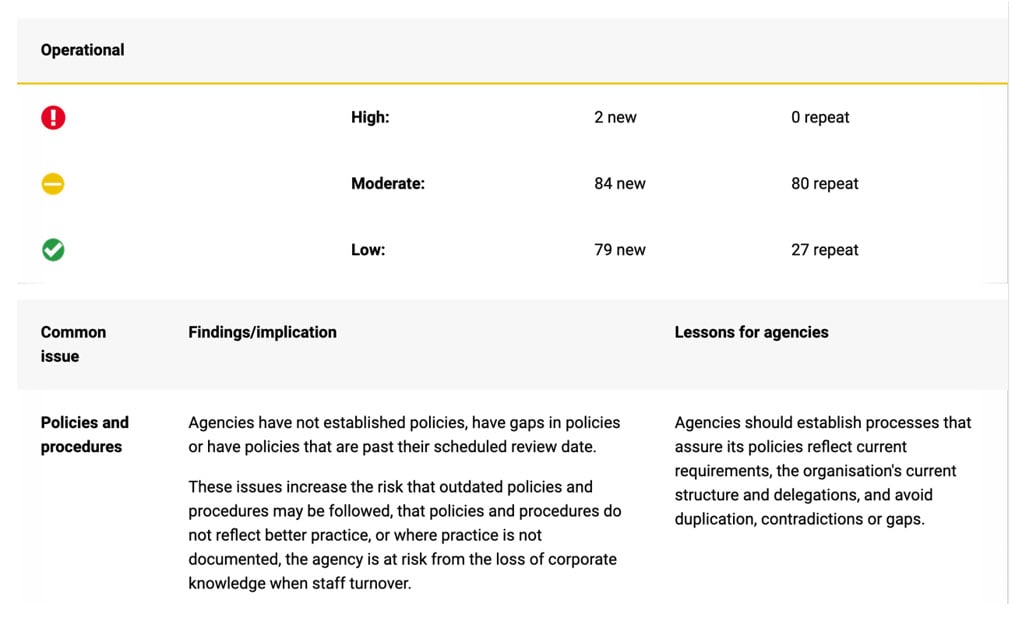
Here are the top 8 common audit findings across a group of government
(NSW, 2019)
- User access administration deficiencies at 58% of clients related to granting, review and removal of user access
- An absence of privileged user activity reviews at 35% of clients
- Password controls which did not align to password policies at 20 per cent of agencies
- Out of date policies or an absence of policies to guide appropriate access decisions
- Poor record keeping and document retention
- Incomplete or inaccurate centralised registers or gaps in these registers
- Policies, procedures or controls no longer suited to the current organisational structure or business activities
- 68% of clients maintain an inventory of their sensitive data and where it resides. However, these inventories are not always complete, and risks may be overlooked
Failing to prepare, is preparing to fail – Get set for success
One of the most prevalent reasons for audit failure is related to the control of user access. To address this, there needs to be a mechanism to understand not just who has access, but equally or more importantly, why they have access. If we can do this in an automated fashion, we can then satisfy the audit control robustly and simply.
How can Torsion help?
By continually tracking access in the background and monitoring who has access to what, Torsion will intelligently detect anomalies and vulnerabilities, flagging any issues to the right people. Using advanced machine learning, Torsion will automatically determine who has access to information and bring any potential vulnerability to the attention of the file/directory/SharePoint site owner for review. If they agree there is a problem, Torsion fixes it.
Rather than manually compiled groups to control access, Torsion can have a simple rule such as “Anyone in Marketing or Sales in Boston or Sydney and a Director” can have access. Then, as people change roles and move around, who has access to important files, folders, Teams and sites is updated automatically and accurately. Access doesn’t have to be immediately revoked, it can also be decayed over time to give time for handovers and the like.
By creating simple rules and policies such as these to control who is permitted access to different types of information, Torsion will identify if a user attempts to share information with someone inappropriate and actively prevent the share. Integrating seamlessly into SharePoint, Teams and more, when someone shares a file or site, – could be their job role or department, the account they are working on or even covering for a colleague on leave.
Example – Re-audit without Torsion, Steve in finance shared a file with Erika in Payroll, which at the time of sharing the information was a fair and reasonable thing to do. However, Erika now leaves Payroll and moves into Marketing to do something “a little more exciting”. Erika’s access to Finance remained. At the time of the audit, processes for managing staff moves were not in place and/or had not been executed. As a result, the business had no idea of the resulting risk or no way of knowing why the access was granted (Oxygen for an Auditor).
The problems identified in this scenario, are at a minimum, 1. The reason for sharing the file was not captured, and 2. Once Erika changed roles, no notification of the role change and or management of the resulting stale access was provided and therefore her access was not revoked.
Let’s add Torsion to the equation
With Torsion in place, prior to Steve sharing the file, or location, he asked Torsion to create a rule which only allowed individuals in the Payroll team to have access and to revoke all other access. Now, when Steve attempts to share the file with Erika, he is asked for a “reason for sharing” and provided with an option to set a “time period” for which access will be available. All the time Erika remains in Payroll her access is valid for the time period granted. However, when Erika moves to Marketing, the business rule created by Steve is broken because her role is no longer in Payroll, and immediately, Steve is notified of the change as the data or site owner, and can choose how he wants to manage access to the file (decay over time or revoke immediately).
Now Steve is aware of the issue, he can get even more creative and go beyond just Payroll and ask Torsion “Show me all users in “my office location”, with “finance” in their job description or title, who have access to this file location. Steve will then be provided with a list of users who meet the criteria, together with those who have access, but do NOT meet the criteria. This is where is gets interesting, as control is now very much in Steve’s hands. With this new level of visibility, access control and information governance become very manageable and with the power in the hands of the business units who own the content, Steve becomes very well equipped to deal with the Re-audit process and can solve for the number 1 problem (granting, review and removal of user access) very .
In Summary
Moving from “Re-Audit” to “Pre-Audit” can be achieved in an effective and controlled manner, without the typical “flurry of activity” and poor decisions made post audit. Adding Torsion to your arsenal can help you get grounded with Information governance. Getting into this position of power is rewarding both personally, and professionally as you now have one less thing to worry about and can be confident in your ability to respond to audit requests both internally and when forced upon by external parties. Furthermore, once Torsion is in place, the “Oh my g-d we have an audit coming up” disappears from your vocabulary. You can be confident in knowing the right people have access to the right files for the right timeframe. No longer does IT need to be held accountable for what really is a business decision.
Want to see this in action?
- Click here for access to our “canned” demo
- Register here for your Proof of Value
- Contact us for more information